Tennessee-based security firm provides access control solutions to HOPE Family Health and puts the security needs of patients and staff members first.
Certification of iSTAR Edge and iSTAR Ultra broadens company's range of government-compliant products.
SMS access control technology helps Crider gain highest level of food safety certification.

The late night host was able to get passwords from strangers off the street in a skit on his show.
- By Matt Holden
- Jan 20, 2015
New website includes different areas with customized content for dealers, system users and consultants.
Central Station Alarm Association’s certification re-enforces Protection 1’s commitment to providing the highest level of service to its customers.
No penetration of bullet-proof guard booth in November 28 downtown Austin, Texas shooting.
World's oldest programs for design excellence worldwide that receives several thousand submissions from 48 countries across the globe.
Helps to shape physical access control smart card technology in concert with other committee and Smart Card Alliance representatives.

Armed boats and police dogs are just a couple of the ways officials are protecting the trial.
- By Matt Holden
- Jan 09, 2015
iTRUST 2.0 POE+ powered, server-less, IP access control product launches and promoted in Metro New York, New Jersey and the New England area.
Secure, wireless, battery-operated, electronic lock that works with company's software for easy management of networked access control.
Company provides IP, wireless and battery-powered access control solutions, providing electronic security for any site requirement.
Card-based access control systems fight skimming, eavesdropping and relay attacks.

Some of the biggest holes in airport security revolve around those that work there.
Company entering 30th year with new name, logo, color scheme and tag line.

In an effort to serve its students, the university recently conducted a pilot program with HID Global of Austin, Texas in which approximately 15 participants used their smartphones to open doors at one or more of six possible campus entry points, including one parking garage.
- By Deb Spitler
- Jan 01, 2015
Access control solution blends advanced wireless keyless access control convenience in a customizable designer locking form factor.
Updated 9600 Series is stronger and sleeker while new magnetic template, the 9000-MTK makes installations easier.

The report also suggests that the Secret Service needs a new director from outside the organization
- By Matt Holden
- Dec 19, 2014
Security insight & business intelligence platform has integrated feature & request customer feedback portal.
Decorative bollards stop 15,000 pound (6,800 kg) vehicles traveling 30 mph (50 kph.
Freedom CUBE delivers enterprise-class capabilities for small-to-medium businesses.

Pakistani militant group stormed military-operated school in Peshawar, opened fire, mostly killing students. (WARNING: Disturbing recollection from 16-year-old student included.)
- By Ginger Hill
- Dec 16, 2014
Building on its success in the installed smart home space with the Linear and 2GIG brands, Nortek prepares the GoControl brand for entrance into the DIY smart home category.
Mechanical and electronic locking plus enterprise access control ensure solutions address all budgets and applications.
R4-EM 8 Series combines the efficient, robust performance of a rotary latch mechanism with simplified DC motor actuation.

Airport and border screening are exempt from the new rules.
- By Matt Holden
- Dec 08, 2014
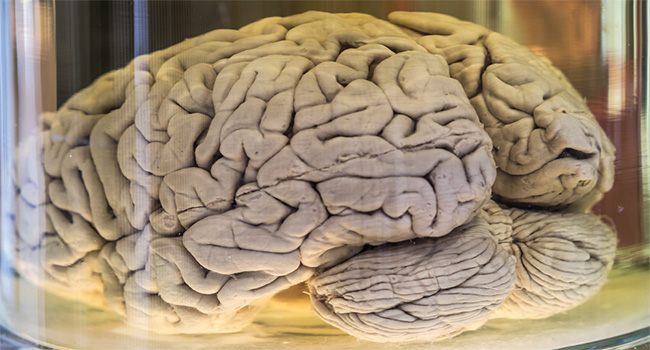
This is roughly half of the specimens the university had in a collection.
- By Matt Holden
- Dec 03, 2014
Lock or disable groups of doors with a single command to react to internal or external threats.
Improves customer experience and parking enforcement efficiency for cities, education and retail customers.
Integration cooperatively tested and certified.

From 4K Ultra HD resolution surveillance cameras to near field communication (NFC) or Bluetooth-enabled access control readers and applications, technology innovation in the security industry runs the gamut.
- By Jeremy Krinitt
- Dec 01, 2014
Assessment of video surveillance, access control and intruder alarm markets for 2014 and analysis of growth to 2018.
From retrofits to regular doors and elevators, wireless locking systems are becoming ubiquitous for a wide variety of installations.
- By Scott Lindley
- Nov 24, 2014
Up to 20-inch (508 mm) read range offers easy access from doors to turnstiles and parking gates.
New strategic enterprise application partners include Jetmobile and Ricoh China.
Command and control platform fully integrated with A1001 Network Door Controller.

Protecting on-site assets and facilities by limiting access to buildings, vehicles and pooled assets.
- By Danny Garrido
- Nov 21, 2014
Company represented in NYC area and Northern New Jersey by manufacturer's representative.