The MasterCard Card Quality Management audit covers HID Global’s contactless and dual interface inlays for banking and payment solutions.

Three California inmates who escaped from a maximum security facility have been recaptured. Now the investigation focuses on how it happened.
- By Sydny Shepard
- Feb 01, 2016

The remote geographic location with each island being separated by miles of ocean posed some challenges for the project, making air, land and sea transportation necessary to complete the job.
- By Kim Rahfaldt
- Feb 01, 2016

The daily increase in the number of cyber attacks launched and the success hackers are having against heavily guarded businesses are a wake-up call for all companies to be more proactive and vigilant in their security efforts.
- By Gregory Grant
- Feb 01, 2016

Successful companies read the tea leaves and saw IoT-connected devices coming. This includes video surveillance, which is now among the fastest growing industries in terms of data generation and adoption of new data storage technologies.
- By Brian Grainger
- Feb 01, 2016

Because of recent news and my frequent visits through the security checkpoint, I have come to lack confidence in TSA employees.
- By Ralph C. Jensen
- Feb 01, 2016

For many years, physical and network security existed as separate disciplines, each managed by an independent operations team on its own side of the house with little or no crossover between the two.

Every summer, the Saratoga Race Course brings thousands of visitors to the City of Saratoga Springs, NY. The revenue generated during the racing season boosts the city’s economy for the rest of the year.
- By Courtney Dillon Pedersen
- Feb 01, 2016
Thirty years ago, maybe more, the dream of the IP camera was about to make its debut. The technology, as I remember it, wasn’t all that well received, but that didn’t mean it was a bad idea. It became an exercise of marketing the future to the here and now.
- By Ralph C. Jensen
- Feb 01, 2016

In the past two years several high profile data breaches, namely the Target data breach in 2014, have put greater focus on the data security of all network connected devices.
- By Brian Carle
- Feb 01, 2016
Have you ever stopped to notice that as video surveillance goes, so goes the security industry? Nowhere is that more evident than in the major shift from analog to IP technology.

We almost never think about the fact that the public flows through our banks day after day or that suppliers and partners are in and out of branch locations, some requiring access to sensitive areas, all the time.
- By Scott Thomas
- Feb 01, 2016

Each industry has its own specific requirements for photo ID card solutions. The guidelines used by each market vary depending on the type of badges that companies need to print and the frequency.
- By Monique Merhige
- Feb 01, 2016

You are on duty at a large power station when you hear a gunshot coming from the South side of the facility. This shot triggers your security systems sniper detection alarm.
- By Brittany Lauridsen
- Feb 01, 2016
Pivot3, a pioneer and innovator in the development of hyper-converged infrastructure, announced that it will acquire NexGen Storage, a privately held leading provider of hybrid storage appliances, dynamic all-flash arrays and Quality of Service capabilities.

All in all, cyberattacks will continue to menace financial institutions in 2016.
- By Hagai Schaffer
- Jan 27, 2016

Protesters who’ve occupied a federal building in Oregon have been arrested.
- By Sydny Shepard
- Jan 27, 2016

Consumers may think data breaches are inevitable, but if a business can show them that such risks are avoidable, it’s sure to profit. Don’t get left behind by your competitors—invest in a robust payment-protection platform before it’s too late.
- By Michael Thorne
- Jan 27, 2016

Johnson Controls strikes $20 billion Tyco Acquisition, company to be based in Ireland.
- By Sydny Shepard
- Jan 25, 2016

California officials are asking for the public’s help to find three inmates who escaped from jail.
- By Sydny Shepard
- Jan 25, 2016
As we do more with our phones and increasingly demand anywhere/anytime on-line access, there is the opportunity to better protect these activities while creating a more satisfying, mobile-centric security experience at home, in the office, on the road and on-line.
- By HID Global Innovation Team
- Jan 25, 2016

Lots of companies, even the White House, use a conference calling system that could possibly be tapped by hackers, according to new research.
- By Sydny Shepard
- Jan 22, 2016
Pelco by Schneider Electric Announces Integration of Optera and Spectra Camera Ranges with Genetec Security Center

You still can’t bring your loaded gun onto a plane, 2015 proved that.
- By Sydny Shepard
- Jan 22, 2016
Schools across the northern states are reacting to threats of bombs and mass shootings.
- By Sydny Shepard
- Jan 19, 2016
Peter J. O'Neil has joined ASIS International as Executive VP and CEO
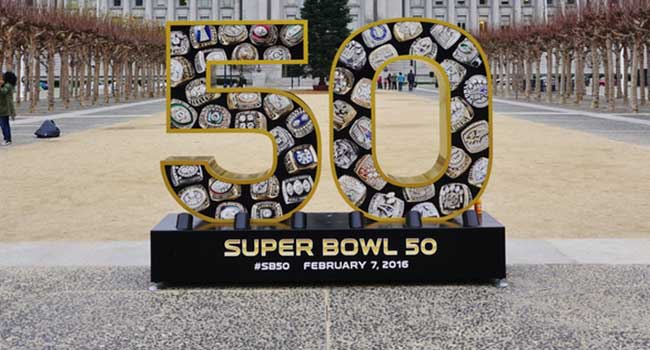
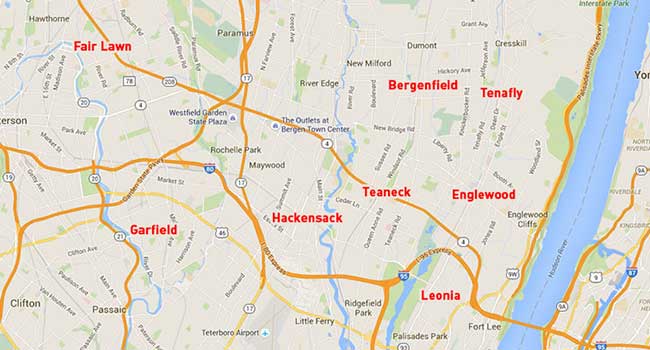
Federal officials mull whether attack on fiber optic systems are connected to a plot against the Super Bowl.
- By Sydny Shepard
- Jan 19, 2016

A student discovered that wearable technology could lead to stolen ATM pin codes.
- By Sydny Shepard
- Jan 15, 2016
In her new position, Doyle will be responsible for managing new and existing accounts as the company continues its growth in the region.
Digital Watchdog released information announcing the integration of the company's powerful DW Spectrum IPVMS with RBH Access Integra32.