
- By Matt Holden
- Aug 13, 2015
A thriving center of culture, cowboys and commerce.
Benefiting Mission 500 effort to help US kids in poverty.
Partnership enables organizations to easily scan code and eliminate software risk.
Single and dual voltage, wall and rack options can supply power to iSTAR door controllers, locks and other auxiliary equipment.
Introducing the neXus XCR100 2.0 card printer for over-sized photo ID badges.
Easier to use and offers a variety of feature enrichments, including support for a variety of foreign languages.
Surveillint 8 features a unique intelligent alarm triggering capability, SMS and MMS integration for cost effective mass notification, and a tool for fast Enterprise Dashboard deployment.
Combines sixty years of industry experience.

Security market to see rise of opportunities in cloud data center security.
- By Ginger Hill
- Aug 12, 2015

The Indiana Department of Administration wants to install the turnstiles at Statehouse entryways.
- By Matt Holden
- Aug 12, 2015

Since 2010 high-ranking officials' vacation plans, emails to friends and other correspondence has been targeted by China.
- By Ginger Hill
- Aug 11, 2015
New partnership helps ensure data integrity and operational continuity if a cyber-incident occurs.
Flexible, cost-efficient pin pad token solution for financial and enterprise deployments.
Capable of powering dual displays in Ultra HD resolution through HDMI and JAE TX25 connector.
Siklu to provide wireless connectivity via tiny, interference-free Gigabit radio, the EH-600T.
UL-listed and NFPA-compliant, features compact, intelligent Fire Alarm Control Panel (FACP) for wet or dry fire sprinkler systems.
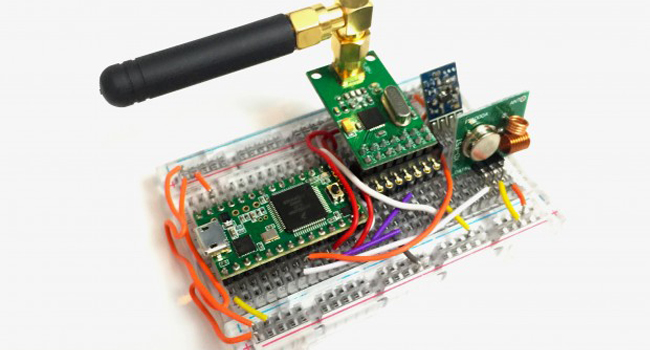
Small $30 device - Rolljam - enables entry into two of your most private places.
- By Ginger Hill
- Aug 10, 2015
Visitors can explore features and benefits by seeing NVRs, cameras, and monitors in action, first hand.
Newest DirectIP integrations enhance IDIS’s ability to meet customer needs for seamless security solutions.
BB&T Ballpark ensures the finest guest experience while protecting its newly-built $55 million facility from threats with unified video surveillance and access control.

Maintaining a secure environment with proven technology to assist in reducing crime and speeding up investigations.
Amulet Ballistic Barriers New ‘T’ Kit protects moviegoers from active shooters.
Represents company's strong commitment to Canadian market.
Enables monitoring centers to leverage cloud services, including Video Verification, 24/7 Live Intervention, Virtual Guard, Virtual Escort, and Virtual Assistant.
To deliver agentless endpoint security to French market.
Provides common video interface for a wide range of vertical market applications.
Enhances awareness, response time and operational efficiencies.
Partnership to incorporate secure microcontroller IC in new ultra-thin Polycarbonate (PC) ePrelaminate inlay solution.

Nearly 1/3 of moviegoers in America are willing to endure metal detectors and pat downs to ensure a safe movie experience.
- By Ginger Hill
- Aug 07, 2015