
Last weeks wave of Bomb Threats has been linked to the same group of spammers responsible for mass sextortion scams.
- By Sydny Shepard
- Dec 18, 2018
Facebook continues to face criticism of the information they share with third-party app developers.
- By Sydny Shepard
- Dec 17, 2018

Private investigators believe Chinese hackers may be to blame in the Marriott hack.
- By Sydny Shepard
- Dec 11, 2018

Users can enable a feature in the preview version of Safari that lets them log in with USB-based CTAP2 sticks, which offer more stringent protection than a standard text-based password.
- By Jessica Davis
- Dec 07, 2018

Mozilla and ThingsCon announced Thursday the launch of the Trustable Technology Mark, designed to help customers tell if an Internet of Things-connected device is designed with strict privacy and security measures.
- By Jessica Davis
- Dec 07, 2018

Simply employing the most basic of information security rules will make you and your business more safe and secure.

The names, email addresses and passwords of 100 million users of Quora have been made vulnerable.
- By Sydny Shepard
- Dec 05, 2018

Video surveillance has dramatically changed in recent decades. Open, IP-based network technology has largely replaced the closed, proprietary world that long dominated the security industry.
- By Jeff Whitney
- Dec 01, 2018

The coffee chain says hackers might have accessed customer info through a data breach.
- By Sydny Shepard
- Nov 30, 2018

Legacy endpoint prevention and protection solutions are limited when faced with advanced and sophisticated threats
- By Liviu Arsene
- Nov 30, 2018

Huawei, the world’s biggest producer of telecoms equipment, has faced pushback from governments due to concerns that its technology could be used for unsavory purposes such as spying.
- By Jessica Davis
- Nov 29, 2018

Here are five principles that developers should keep in mind to create more secure apps
- By Madhan Kanagavel
- Nov 29, 2018

Tips and tactics for ensuring your small business is safe from the threat of cyberattacks.
- By Michael Flavin
- Nov 28, 2018

A security hole in a mail preview program may have made the data of 60 million customers vulnerable.
- By Sydny Shepard
- Nov 28, 2018

How a 10-minute survey cost Facebook $150 billion
- By Colin Earl
- Nov 27, 2018
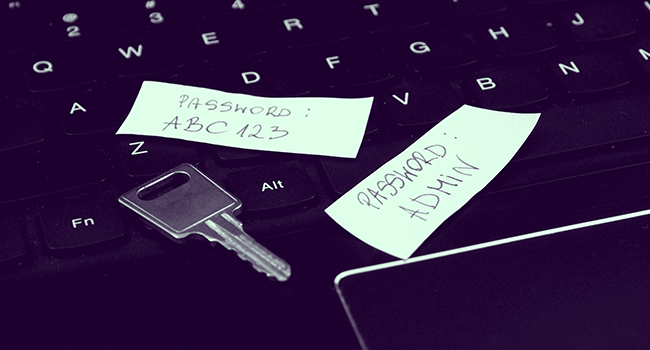
According to the survey, three of every four respondents admitted that they reuse passwords across accounts, an increase from the 56 percent of respondents who admitted the same in the survey’s 2014 edition.
- By Jessica Davis
- Nov 26, 2018

Internet connected devices might be the hot item for Christmas this year, but are they secure?
- By Sydny Shepard
- Nov 23, 2018

Recommendations for safe online holiday shopping - a cybersecurity perspective.
- By Sydny Shepard
- Nov 23, 2018
- By Tyler Reguly
- Nov 21, 2018

Beware holiday shoppers. Attempts at fraud will peak on Thanksgiving Day this year.
- By Sydny Shepard
- Nov 21, 2018