
A University of Kansas student was able to use a keystroke logger to gain access to a professor's computers and change his grades.
- By Sydny Shepard
- Oct 17, 2017

The hole in Wi-Fi security affects the vast majority of Wi-Fi devices and networks.
- By Sydny Shepard
- Oct 16, 2017

Oops!...Equifax did it again.
- By Chris Olson
- Oct 16, 2017

According to a new study, 70 percent of employees cannot grasp web security and privacy.
- By Sydny Shepard
- Oct 12, 2017

Yahoo recieved new information to show that all the accounts had been hacked, not just a portion as previously thought.
It seems we can’t go a single day without a new data breach making headlines.

Today, cloud applications are all the rage and for good reason. The cloud allows us to work and play in ways that are so much more productive and engaging.
- By Nicholas Maier
- Oct 01, 2017

As new technologies emerge, ever-vigilant fraudsters remain hard at work searching for and exploiting system weaknesses before they can be patched.
- By Michael Lynch
- Sep 29, 2017

The grocery chain has "recieved information reguarding unauthorized access of payment card information."

Equifax says the two breaches are unrelated.
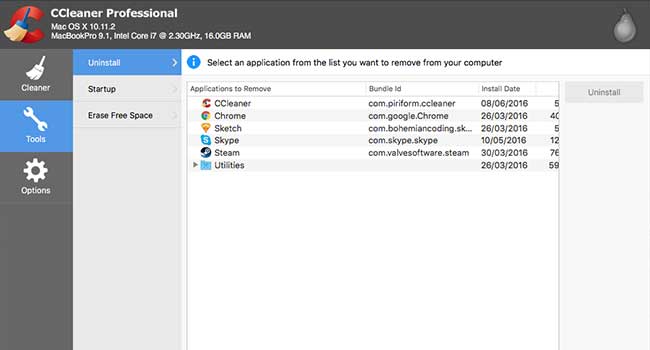
Hackers have hidden a backdoor in a security application called CCleaner. So far it has 2 billion downloads and has infected 2.3 million people and counting.

Breakthroughs in technology mean that connected cars are shunning physical keys in favor of digital, smartphone-based entry systems.

The US government has officially banned the use of Kaspersky security software in all of its federal agencies.
A set of vulnerabilities present in "almost every" device with Bluetooth capabilities has been revealed by researchers at security firm Armis.

The iOS 11 has been in beta testing for a few weeks now and many users are reporting a new discovered security feature that could boost a user's data security and make it harder for police to find information.

A recent incident in upstate New York has shown that even police departments aren't immune from hacking.

The Atlanta-based company announced the hack on Thursday, and said that intruders were able to access customers' Social Security numbers, addresses, names, birthdays, driver’s license numbers and more.
- By Nicole Crites
- Sep 08, 2017

Gaping security holes have been discovered in most AT&T U-verse cable modems that would allow remote cyber criminals to access a household’s internet connection as well as any devices connected to it.

Moving to higher ground within the commercial enterprise space.
- By Gerald Hubbard
- Sep 05, 2017

The Facebook-owned social media company sent an email to high-profile users on Wednesday alerting them that a bug in its software may have allowed users’ account data to be accessed.