
Messaging app, WhatsApp, has made a move to encrypt all messages sent and received on their platform.
- By Sydny Shepard
- Apr 06, 2016

The Panama Papers, recently leaked by an anonymous source, is the biggest data breach in history.
- By Sydny Shepard
- Apr 04, 2016

There going to be a ton of new products at this year’s ISC West show, especially internet driven devices.
- By Sydny Shepard
- Apr 04, 2016

When it comes to cybersecurity the world falls into two camps: those focused on securing their hardware and applications as a closed system, and those who recognize that converging technologies calls for a more ecosystem-centric approach.
- By Vince Ricco
- Apr 01, 2016

After the FBI was successfully able to use a third party source to extract the data from the San Bernardino attack’s phone, they are now offering to help in other cases.
- By Sydny Shepard
- Mar 31, 2016

While banks have been in compliance with the new standardized EMV chip in debit and credit cards, retailers and consumers just don’t care.
- By Sydny Shepard
- Mar 29, 2016

Nearby nuclear plants have been a focus of the Brussels terrorist attacks as some fear they could be vulnerable to attack.
- By Sydny Shepard
- Mar 25, 2016

Yet another hospital was tossed into chaos after its computers were infected by hackers.
- By Sydny Shepard
- Mar 24, 2016

Apple was thought to have caught its first break in a long fight with the FBI that includes the iPhone of one of the San Bernardino attackers.
- By Sydny Shepard
- Mar 24, 2016

There are many security risks that could come up by allowing citizens to vote online, but Utah is going to try it anyway.
- By Sydny Shepard
- Mar 22, 2016

Despite the fact that bad passwords are becoming a dying breed because of the immense security measures one must comply with in order to create a password to login to an account, sports fans have found a way to use their favorite games as terrible credentials.
- By Sydny Shepard
- Mar 21, 2016

The Department of Homeland Security began sharing details of digital threats with private business to improve cybersecurity.
- By Sydny Shepard
- Mar 21, 2016

New tests by German vehicle experts show that 24 cars from 19 different manufacturers are vulnerable to an “easily built” electronic device.
- By Sydny Shepard
- Mar 18, 2016

Hackers have adopted a number of attack methods, which include combinations of social engineering attacks, malicious mobile applications, phishing scams, and ransomware, to name a few.
- By Lance Mueller
- Mar 17, 2016

MasterCard has already announced they are looking to implement the new technology, but now so is Amazon.
- By Sydny Shepard
- Mar 15, 2016
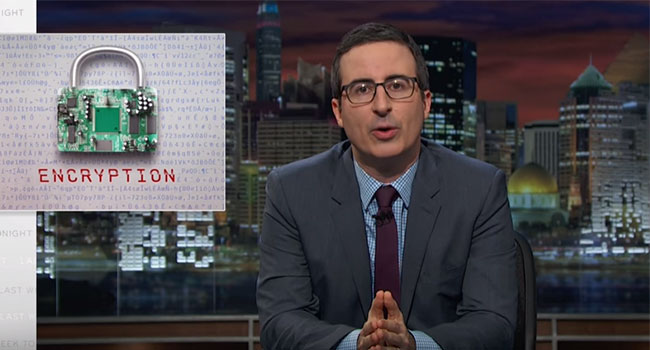
TV show host, John Oliver, used his platform on Last Week Tonight to help others understand the Apple vs. FBI debate.
- By Sydny Shepard
- Mar 14, 2016

A hacker has created an online database that anyone can search in order to receive the names, birth dates and home addresses of Miami municipal workers.
- By Sydny Shepard
- Mar 09, 2016

Dell commissioned a survey to obtain a comprehensive look at how decision makers in the mid-market – as well as the C-Suite – view data security trends.
- By Sydny Shepard
- Mar 08, 2016

Researchers say that police drones used for surveillance can be hacked with a rather inexpensive kit.
- By Sydny Shepard
- Mar 04, 2016

Today’s retail banks are nothing like they were in your grandfather’s day. Back then customers conducted all their banking business in a physical branch.
- By Stephen Joseph
- Mar 01, 2016