
The 2015 edition of the DBIR provides insight into the state of cyber-security in 2014.
- By Matt Holden
- Apr 22, 2015

With so many business functions becoming integrated through networked devices or systems, it is no wonder that one of the newly re-introduced buzzwords spreading throughout the physical security industry is integrated security services.
- By Cale Dowell
- Apr 10, 2015

An official has stated that unclassified computers at the White House are vulnerable.
- By Matt Holden
- Apr 08, 2015
Convergence of physical and cybersecurity along with information management solutions.

A cybersecurity activist developed the roster, but it has flaws.
- By Matt Holden
- Apr 01, 2015
Highly malicious strain found only takes 1 click to infect systems using DropBox.

Per Björkdahl shares his thoughts about cybersecurity, the IP video market, access control and interoperability.
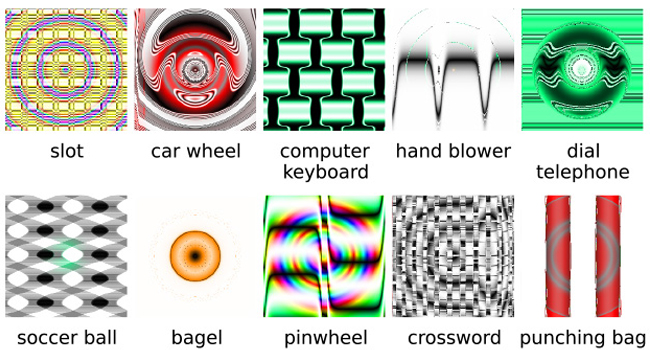
Machines learning to recognize objects with accuracy, but can also be fooled by optical illusions.
- By Ginger Hill
- Mar 25, 2015

A flaw was discovered in the Hilton HHonors program that could let anyone hijack all accounts.
- By Matt Holden
- Mar 24, 2015
Cyber security and cyber space technology has become one of Israel's most important exports.
Rewards start-ups for their innovation in the smart home vertical.

Causing fraudulent charges to appear on credit cards and users being locked out of accounts.
- By Ginger Hill
- Mar 19, 2015

New Jersey recently switched to digital testing, bringing a host of new security concerns with it.
- By Matt Holden
- Mar 17, 2015

Malware activated as soon as the device is plugged in; no further action required.
- By Ginger Hill
- Mar 16, 2015

The social networking site explains why it might or might not remove a piece of content reported as inappropriate or offensive.
- By Matt Holden
- Mar 16, 2015
We don’t know much yet, but Apple has shown a few features that will help keep your information safe.
- By Matt Holden
- Mar 11, 2015

There are steps anyone can take to ensure hackers will have a more difficult time accessing your system
- By Matt Holden
- Mar 10, 2015

The player accidentally swapped laptops with a principal while going through security.
- By Matt Holden
- Mar 09, 2015

A misconfigured encryption system left it vulnerable to hacking.

Cost is in the billions but only addresses a narrow range of security issues.
- By Ginger Hill
- Mar 04, 2015