
On March 25, before the full impact of coronavirus hit home and the world was still full of hope, Google News showed an eye-wateringly appealing headline: Cybercrime Gangs Promise to Stop Attacks on Healthcare Organizations During the COVID-19 Crisis.
- By Kevin Deierling
- Dec 07, 2020
It’s no surprise that cyber security defenses took their first cues from the physical world. Castles have moats. Your house has a door with a lock. It makes sense to protect your network with a firewall. But cyber criminals soon crashed that plane.
- By Karthik Krishnan
- Dec 03, 2020

The holiday shopping season is here, let’s not forget that we are in COVID-19 pandemic and health officials continue to repeat their messages about the importance of masks, adequate social distancing, and frequent handwashing.
- By Patrick V. Fiel
- Dec 01, 2020
CyberNews.com’s Investigations team today announced that they have identified hidden backdoors in Chinese-manufactured routers that share common firmware, with evidence that the routers are being exploited by the Mirai malware.
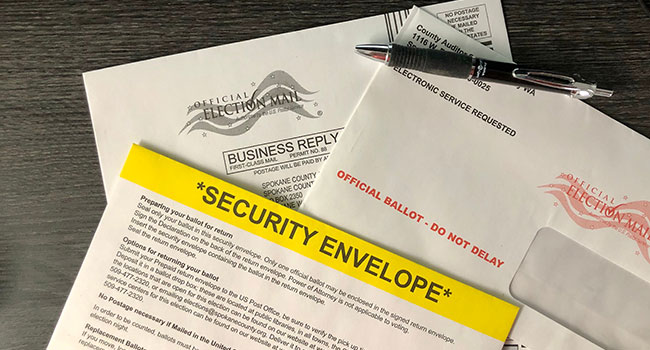
Here is a Q&A that answers questions about spoofing the voter. The answers come from Chris Krebbs, CISA director.
In an open letter to Twitter CEO Jack Dorsey, Department of Homeland Security (DHS) Acting Secretary Chad F. Wolf today called on Twitter to no longer obstruct Americans’ unalienable right to communicate with each other, their government, and its officials on the platform, because doing so endangers the national security.

The most recent elections is the most secure in the nation’s history. Or, is it? Government officials say it is the most secure ever.

The 2020 election season is a Big Deal as well it should be. The Vote, as foundational parts of the whole, is complicated in practice with history showing us just how complicated it can be. Protecting the process and making sure the Vote is fair, secure, and timely, is vital to American Democracy.
- By Saryu Nayyar
- Oct 28, 2020

The Trump Administration continues its work to ensure America’s technological and innovative edges are guaranteed by offering the first National Strategy for Critical and Emerging Technology.

The recent release of a massive cache of sensitive Law Enforcement data has been in the news recently. The trove of roughly 270 gigabytes of data posted to the Denial of Secrets website has been referred to as “BlueLeaks.”
- By Nilesh Dherange
- Oct 13, 2020

According to data presented by the Atlas VPN team, there are 78 new cybersecurity companies founded in 2020 that cumulatively have raised over $31.6 million in funding year-to-date.
Crowdsourcing effort to uncover security issues is latest addition to company’s broader cybersecurity strategy
Due to the nature of cyber-physical systems (CPSs), incidents can quickly lead to physical harm to people, destruction of property or environmental disasters. Gartner analysts predict that incidents will rapidly increase in the coming years due to a lack of security focus and spending currently aligning to these assets.
With digital transformation comes the move to the cloud. What many businesses don’t realize is that it requires a retooling of their security strategy from the ground up.
- By Eric Kedrosky
- Sep 15, 2020
McAfee today announced its latest consumer security portfolio that includes enhanced products with better user experiences such as a native VPN and new features, including integrated social media and tech scam protection.
According to the Confidential Computing Consortium: “Confidential computing is the protection of data in use using hardware-based Trusted Execution Environments (TEE).
- By Richard Searle
- Sep 14, 2020

The Security Industry Association (SIA) has released its new policy principles guiding the development and deployment of facial recognition technology.
The Trump Administration announced the first comprehensive cybersecurity policy for systems used in outer space and near space Sept. 4.
Many of the cyberattacks on state, local, tribal and territorial governments are not complicated and could be avoided through simple steps such as improved cyber hygiene and two-factor authentication, a new report states.
- By Stephanie Kanowitz
- Sep 08, 2020

Video surveillance is commonplace today, but many organizations don’t even realize that they aren’t fully leveraging the video data that their cameras capture. Traditionally, law enforcement and physical security teams use video cameras to monitor areas in real-time and to review footage to glean evidence for post-incident investigation.
- By Stephanie Weagle
- Sep 03, 2020