
It is the time of year for reflections, resolutions, predictions and lists. News stories about trends are everywhere, with tips about getting businesses on track for success in 2022.
- By Dean Drako
- Jan 27, 2022
Artificial intelligence (AI) enables machines to learn, understand, and act accordingly – giving it enormous potential.
- By Paul Garms
- Jan 27, 2022

The IoT presents a huge opportunity market. Every second, 127 new IoT devices are connected to the web, and experts predict that by 2025, that figure will equate to more than 75 billion connected devices overall. Unfortunately, this volume of connected devices brings inevitable security risks.
- By Alexandre Araujo
- Nov 29, 2021

In banking today, the FBI and Federal Deposit Insurance Corp. (FDIC), have mandated security standards that require a minimum number of cameras and camera resolution in each facility.
- By Paul Fisher
- Nov 22, 2021

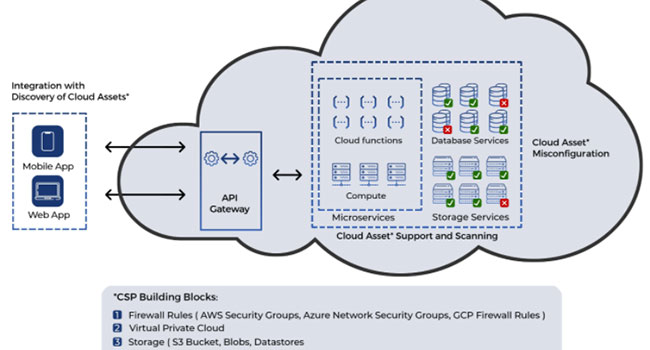
The security approaches we counted on to secure our networks and protect our IT resources against attackers are no longer up to the task.
- By Michael Wood
- Nov 02, 2021

It was not all that long ago when discussion of professional security services on the Cloud seemed all but preposterous due to bandwidth and security concerns.
- By Laura Worell
- Oct 20, 2021

The Internet of Things (IoT) is turning dumb houses into smart homes. It is also revolutionizing access control systems for all types of commercial buildings, from small offices and retail shops to enterprise campuses and sprawling factories.
- By Shahar Feldman
- Oct 01, 2021

There have been on-going discussions the past several years about how Big Data and Artificial Intelligence (AI) can be used to modernize physical security systems and operations.

Pro-Vigil, a provider of remote video monitoring, management and crime deterrence solutions, recently published a research report that found organizations are more concerned about their Artificial Intelligence (AI)-powered video surveillance system's ability to deter crime than any potential bias issues.

As the Internet of Things (IoT) has continued to evolve, so, too, have the options for pairing smart home integration with both professionally monitored and self-monitored home security solutions.
- By Kelly Atkinson
- Jul 26, 2021
The Security Industry Association (SIA) has announced its strong opposition to the Facial Recognition and Biometric Technology Moratorium Act

Imagine when you know what’s next. You can respond before potential situations occur and anticipate business opportunities that create new revenue streams or reduce operational costs.
- By Paul Garms
- Jun 01, 2021
Not long ago, artificial intelligence was viewed as science fiction. Today, it routinely makes our lives more secure and convenient. AI surrounds us in our everyday lives.
- By Brian Baker
- May 24, 2021

When it comes to device and systems connectivity, surge protection solutions can mitigate risk
- By Chris Ralston
- May 20, 2021
One of our best customers is a Fortune 50 financial services company for homeowners across America.
- By Doug Dooley
- Apr 26, 2021

Cybersecurity experts have long warned of attacks on small municipal systems. Until hackers accessed the water treatment plant of a small Florida city this year, those warnings were “out of sight, out of mind.” Now, both local and national authorities’ perspectives on the dangers of cybersecurity attacks are changing.
- By Jeremy Rasmussen
- Apr 05, 2021

Cloud-based technology and solutions have become more and more mainstream, especially in the commercial security industry.
- By Kim Hartman
- Apr 01, 2021

It is the end of the line for analog phone systems, which can leave alarm companies hanging out to dry trying to figure out if they need to replace costly alarm panels.
- By Monique Merhige
- Mar 29, 2021

As the digital transformation trend continues to highlight business agendas, now more than ever enterprises need infrastructure solutions that enable them to connect more locations at faster speeds.
- By Michael Wood
- Mar 04, 2021

If the pandemic has taught us anything, it’s that secure remote access to systems is no longer a “nice to have” feature.
- By Aaron Saks
- Feb 01, 2021