
The St. Johns County Sheriff’s Office in Fla., needs to add at least 40 more deputies to keep up with calls for service, according to the sheriff.
- By Jessica Davis
- Mar 27, 2019

San Diego’s mosques have tightened security following an arson attack at a mosque in Escondido, Calif., early Sunday morning.
- By Jessica Davis
- Mar 27, 2019

Mobile, Ala., Councilman Fred Richardson calls for increased security at Sage Park following a shooting Friday night.
- By Jessica Davis
- Mar 27, 2019

New proposal creates stricter safeguards against data breaches, protects more private consumer information and enhances data security and reporting requirements.
- By Sydny Shepard
- Mar 26, 2019

Everyone should be changing their Facebook passwords after it was discovered all use passwords have been left unencrypted and searchable in plaintext.

The City of Spokane is looking into rewarding businesses that invest in additional security measures for their properties.
- By Sydny Shepard
- Mar 26, 2019
Certification encompasses Mercury’s entire portfolio and represents third-party validation of the company’s long-standing commitment to quality, on time delivery and customer service satisfaction

Learn about the key factors to pay attention to when selecting a provider of network vulnerability assessment services.

2FA is more secure than single-factor methods only requiring a password, but it's not an impenetrable method.
- By Kayla Matthews
- Mar 25, 2019

DNS leaks can be a surprisingly common issue and are often only noticed when actively looked for.
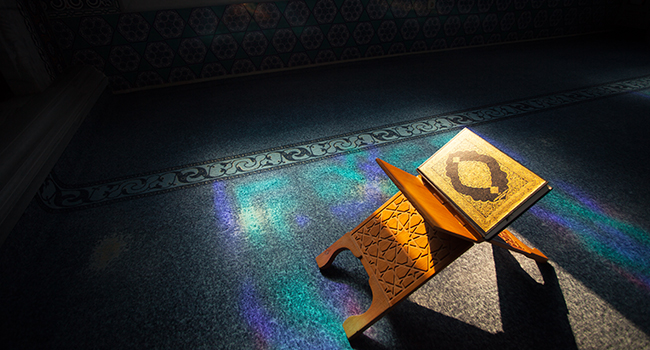
A terror attack targeting Muslims in New Zealand has prompted mosques in Colorado to increase their security indefinitely.
- By Jessica Davis
- Mar 22, 2019

A clear, protective enclosure is being installed this week in the first-floor lobby of Owensboro City Hall as a precautionary measure to protect citizen-service representatives.
- By Jessica Davis
- Mar 22, 2019

Facebook stored “hundreds of millions” of account passwords unencrypted and viewable as plain text to tens of thousands of company employees, KrebsonSecurity reported Thursday.
- By Jessica Davis
- Mar 22, 2019

Austin Police Department plans to beef up downtown security following South by Southwest festival weekend that included five shootings, two crashes involving pedestrians and a suspicious death
- By Jessica Davis
- Mar 21, 2019

Jacksonville, Fla., now has 380 officers on its streets wearing body cameras.
- By Jessica Davis
- Mar 21, 2019

The Capital Improvements Project Committee recommends $52,500 in security upgrades for Somers Public Library
- By Jessica Davis
- Mar 21, 2019