Awards $1000 to University of Maine Student
Empowering Integrators to Maximize Collaboration, Sales and Margins

Washington state’s new cannabis-tracking system was hacked the weekend of Feb. 3, according to the Washington State Liquor and Cannabis Board (WSLCB). Among other information, the hacker stole route information associated with four days of marijuana deliveries.
- By Jessica Davis
- Feb 12, 2018

Relatively new on the market, the iKeyp is a smart safe for everyday use. It is simple to install and easy to connect with via the app on your smartphone.
- By Ralph C. Jensen
- Feb 12, 2018

Beginning in July with the release of Chrome 68, Google Chrome will mark all HTTP sites as “not secure”. The Chrome browser already displays a green lock icon and “Secure” sign in the URL bar for HTTPS-encrypted websites.
- By Jessica Davis
- Feb 12, 2018

You’ll get a real kick out of this security story. It is all about a secure perimeter and access control that is stored in the cloud and a man devoted to those around him.
- By Ralph C. Jensen
- Feb 12, 2018

Ideal for customers seeking an easy to use end-to-end video surveillance solution, WAVE is highly customizable and can create tailored network video solutions for any type of project, on any device.

Consumer Report says its testing found that Roku devices and Samsung Smart TVs have security flaws that make them vulnerabilities to hackers.
- By Sydny Shepard
- Feb 09, 2018
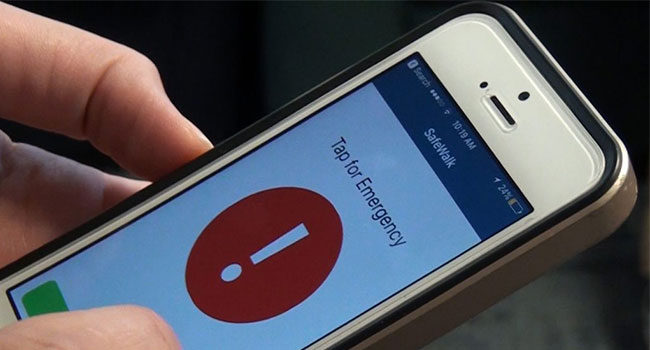
The new university app feature, called Safewalk, expands on an already existent BYU program to enable police to track students’ locations through their smartphones and virtually “walk” with students through campus and the student housing areas.
- By Jessica Davis
- Feb 08, 2018

High acceptance among various verticals including mobile banking and financial services owing to rising security concerns has enhanced biometrics market size.
Leading Connecticut-based turnstile manufacturer starts the year off in the right direction by making it easier for architects & engineers to specify Aeroturn’s solutions.

Soldiers have taken on the work of guarding Pyeongchang's ice area ahead of the Winter Olympics' Opening Ceremony.
- By Sydny Shepard
- Feb 07, 2018

The word "ransomware" has been recognized by the Oxford English Dictionary.
- By Sydny Shepard
- Feb 06, 2018
SALTO Systems has hired Timarron Partners, Inc. to sell and market SALTO’s security products.

Security personnel will be on the lookout for suspicious drones during the Winter Olympics in South Korea.
- By Sydny Shepard
- Feb 05, 2018

The importance of cyber security insurance, and how businesses can increase their privacy to protect themselves against hackers.