
"It is equivalent to the Super Bowl of security."

Work has begun on the clear bulletproof wall that is going up around the perimeter of the Eiffel Tower.
HID Global to acquire Mercury Security in an effort to expand its leadership in Access Control.
Howdy folks, welcome to Dallas! You can’t imagine my appreciation for having ASIS in my backyard. All it means is that I get to stay in my own home and sleep in my own comfortable bed each night. Getting downtown for the tradeshow is a completely different matter.
- By Ralph C. Jensen
- Sep 19, 2017
This year at ASIS 2017, whether you are attending the show in Dallas, Texas or not, you will be able to receive an exclusive look at what is on the show floor from the perspective of our Security Today editors.
- By Sydny Shepard
- Sep 19, 2017
Gerald R. Ford International Airport has received a total of $3.8 million for security upgrades.
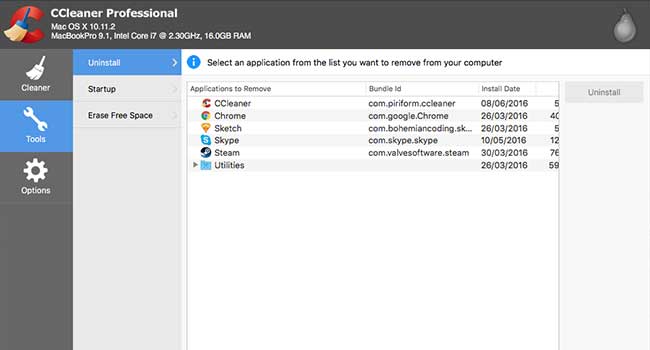
Hackers have hidden a backdoor in a security application called CCleaner. So far it has 2 billion downloads and has infected 2.3 million people and counting.

Protecting physical spaces and facilities is an ever-present problem. As bad actors continue to seek unlawful entry in innovative ways and unforeseeable disasters like fires continue to exist, alarm systems need to keep pace and leverage new technologies to prevent and mitigate these risks.
- By Diego Grassi
- Sep 18, 2017

Breakthroughs in technology mean that connected cars are shunning physical keys in favor of digital, smartphone-based entry systems.

An "improvised explosive device" was detonated on a Tube in south-west London.

The US government has officially banned the use of Kaspersky security software in all of its federal agencies.

One teenage student has died and three others were injured during a school shooting south of Spokane, Washington on Wednesday, Sept. 14.
A set of vulnerabilities present in "almost every" device with Bluetooth capabilities has been revealed by researchers at security firm Armis.

The International Olympic Committee has said there is "no hint" of a security threat for next year's Pyeongchang 2018 winter Olympics in South Korea.

Two Salt Lake City security guards were stabbed early Sunday in a scuffle with customers at a downtown night club, police said.

The iOS 11 has been in beta testing for a few weeks now and many users are reporting a new discovered security feature that could boost a user's data security and make it harder for police to find information.

A recent incident in upstate New York has shown that even police departments aren't immune from hacking.