
When it comes to cybersecurity the world falls into two camps: those focused on securing their hardware and applications as a closed system, and those who recognize that converging technologies calls for a more ecosystem-centric approach.
- By Vince Ricco
- Apr 01, 2016

Business is booming in higher education, and campuses all around the country are stepping up to the challenge to enhance security.
- By Ralph C. Jensen
- Apr 01, 2016
Law enforcement, homeland security, surveillance, emergency response and military operations may span a range of operations, but they all share a crucial need for a detailed, real-time picture of rapidly changing events from various field locations.
- By Eric Chang
- Apr 01, 2016

TelX helps companies build more agile businesses faster with reduced infrastructure complexity and broader reach to new markets.
- By Kim Rahfaldt
- Apr 01, 2016

As a camera views and records in 360 degrees, a circular, distorted image is produced, making it essential to process the image so that the human eye can comprehend the image easily.
- By Jumbi Edulbehram
- Apr 01, 2016

Wireless locks are increasingly becoming the solution of choice in commercial facilities worldwide.
- By Minu Youngkin
- Apr 01, 2016

With almost 33,000 students and just under 5,000 academic and administrative staff, BYU takes its responsibility to provide a secure environment for students, staff and visitors very seriously.
- By Andrew Elvish
- Apr 01, 2016
Now that mobile identities can be carried on phones for physical security applications, they are merging with smart cards into centralized identity management systems.
- By Brandon Arcment
- Apr 01, 2016
A top tier university serving more than 40,000 students needed a cost effective way to improve the level of security at its non-card access controlled doors.
- By Mark Crandall
- Apr 01, 2016

School surveillance continues to be one of the most important markets for video surveillance, And with good reason.
- By Brian Carle
- Apr 01, 2016
You already know you’re going to put some of that expensive security equipment outside in the elements. You also know how brutal the elements can be on sophisticated electronic solutions.
- By Ralph C. Jensen
- Apr 01, 2016
As any security dealer or integrator knows, there are two revenue results of making an access control sale: the proceeds from the original sale itself and the potential recurring revenue that can be wrought from the sale down the road.
- By Scott Lindley
- Apr 01, 2016
Providing Even More Dealers, More Features & Cost-Savings
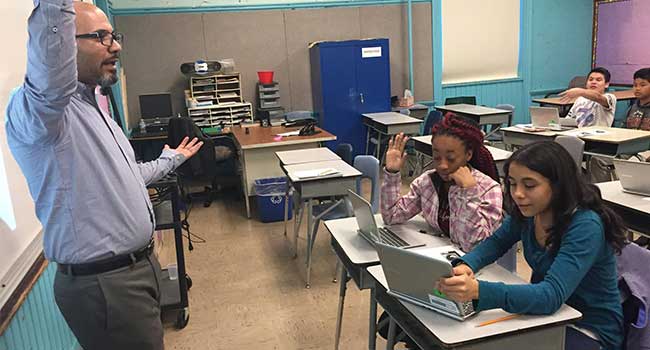
Citizen Schools mobilizes teams of educators and volunteers to lead real-world learning projects and provide academic support, helping students discover and achieve their dreams.

After the FBI was successfully able to use a third party source to extract the data from the San Bernardino attack’s phone, they are now offering to help in other cases.
- By Sydny Shepard
- Mar 31, 2016

Konica Minolta has entered into a share transfer agreement with MOBOTIX.

Guns will not be allowed into the Republican convention in July despite the ideals of those attending.
- By Sydny Shepard
- Mar 30, 2016
Vanderbilt has made a number of hires for its global executive leadership team