Correctional Facilities Using Iris Recognition To Manage Inmate Populations
L-1 Identity Solutions Inc. recently announced that many jails, prisons and correctional and detention centers are successfully using iris recognition solutions to effectively manage detainee and inmate populations, reduce processing time, increase cost efficiencies and improve safety of officers, prisoners and the public.
California’s Contra Costa County was among the first to implement the complete jail management system from L-1, Omni Jail Management System (Omni JMS), and Missouri’s Jasper County jail implemented Offender-ID for immediate and accurate identification of offenders.
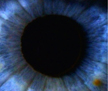
“L-1 solutions are designed in close collaboration with our customers, offering a better solution for accurate identifications and streamlined workflow processes in jail management,” said Rich Agostinelli, president of the biometrics division of L-1 Identity Solutions. “Our iris-based identifications replace traditional methods such as name, designated number, wristband or photo, with an on-the-spot, non-intrusive scan of the subject’s iris, an identifier that is unique to each person and therefore inherently more accurate. With L-1, an arresting or pre-booking officer can quickly and accurately determine the identity of a subject prior to incarceration, and with powerful and time-saving workflow tools like Omni JMS, they can customize and streamline every step of the inmate management process from identification, intake, custody, and eventual release.”
The Contra Costa Office of the Sheriff is a pre- and post-sentence detention operation with more than 2,050 inmates across four facilities. The operation sought a jail management system that could address the need for fast and accurate identification of inmates and control over workflows with a robust system capable of accommodating the flow of arrestees and inmates throughout all its facilities.
Contra Costa rolled out the first Omni JMS implementation in 2008 and after just two months, the county experienced a significant reduction in intake and booking times and errors, including elimination of duplicate data entry for non-integrated systems.
“Thanks to L-1, a jail management system that truly accommodates real-world corrections workflow is now available,” said Captain Sean Fawell of the technical services division of the Contra Costa County Sheriff’s Office. “Before Omni JMS, correctional staff had to work around jail management software. Now, we have a system that is versatile, intuitive and customizable to meet the demanding and dynamic correctional work environment. As a result, our line and support staffs are more efficient and productive. The proper management of inmates and jail operations requires the proper management of costs, staffing and risk, and we are doing just that with the Omni JMS.”
Offender-ID offers the same robust iris technology for offender identification, without the jail management workflow modules. It bolsters the effectiveness of inmate identification, ensuring accurate booking and release by verifying an inmate’s identity at critical junctures of prisoner handling in a jail environment. Jails and sheriff offices in states across the United States including Oklahoma, Colorado, California, New York, Texas and Missouri are all tracking offenders at their facilities using Offender-ID, particularly at intake and release, to improve the safety of officers and the public by reducing the risks associated with mistaken identities.
Jasper County Jail in Missouri first installed L-1’s Offender-ID in August 2007 and has enrolled nearly 7,000 offenders into their database. The L-1 tool helped jail staff thwart multiple incidents of offenders attempting to book in or out under a false ID, forge legal documents, fraudulently obtain medication and steal commissary. The availability of database information on prior arrestees has also helped speed the booking process.
“We have not had a single bad release, nor has this system experienced a failure, since the installation date,” said W. Archie Dunn, sheriff of Jasper County, Mo. “According to my IT staff, it is without a doubt the most stable and reliable application we currently use. I personally believe this technology is the logical next step in the evolution of modern law enforcement. In keeping with the federal government’s push towards multi-modal biometric identification as a means to bolster national security and counter identity theft, iris technology is the perfect partner for our current fingerprint system.”