
Identity: Authenticated
Securing data centers means more than firewalls and encryptions
- By Jon Mooney
- Mar 03, 2010
A data center is a centralized repository, either physical or virtual, used for the storage, management, processing and dissemination of data and information organized around a particular body of knowledge or pertaining to a particular business, usually treated as a mission-critical operation or facility. Just about every company has its own data center. A small local insurance agency calls it a computer system. The insurance conglomerate might call it the computer room. In many instances, the data center is part of a company that provides data services to its customers. The data center market is an important prospect base for building contractors with growth estimated at 11 percent through 2014. The design of new infrastructures needs to provide the ability to scale and adapt to support future needs with near-zero downtime. It involves integrating IT, HVAC, lighting, fire and safety, communications monitoring, control systems and algorithms to process and monitor data. Lastly, data centers require real-time access to local vendor technical expertise with strong reputations.
Getting Centered
Data centers often evolve, migrating from a server closet of less than 200 square feet to a server room with up to a couple dozen servers with no external storage. Next in size is the localized data center of up to 1,000 square feet holding dozens to hundreds of servers with moderate external storage, followed by the mid-tier data center of up to 5,000 square feet with hundreds of servers and extensive external storage. Ultimately, lording over all, is the enterprise-class data center of more than 5,000 square feet with hundreds to thousands of servers and extensive external storage.
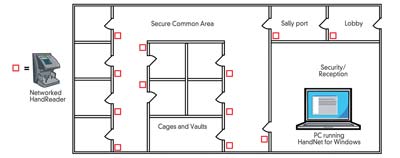
The layout of most large data centers is similar. Users enter a security/reception area to gain access to their system. Upon check-in, they enter the lobby. From there, they go through a sally port to access the secure common area. Upon entering, the door is closed. At the end of the sally port, there is another identification authorization required before they can enter the door to the secure common area. At this point, they can go to their own cage or vault, where they will again be authorized. Most data centers also have similar customer needs. First of all, because of their mission-critical nature, they require a high level of security and typically have a large number of infrequent users. This is especially true of independent data centers. Therefore, the system has to be easy to use but cannot rely on cards that can be easily transferred from person to person.
For offsite storage facilities, the challenges are even greater. They require remote enrollment and multi-facility management in which customers need immediate access—but the security level must remain high.
Security levels range from high to low with the lowest setting only requiring a magnetic-swipe card. The second level of security often requires a PIN or password.
The third level becomes trickier to fool. It checks for what you do. The most common application at this stage is to ensure the user's signature matches the signature on file.
The highest level often involves a biometric. Biometrics identify people by unique human characteristics, for example, the size and shape of the hand, a fingerprint, a voice or several aspects of an eye. A biometric access control reader compares a person's unique characteristics against a previously enrolled image for verification.
Since the challenge in such offsite storage and information-handling facilities has been to provide employees and customers with immediate access while also producing a level of security commensurate with the value of assets being protected, clearly a simple card-based system, where cards can be lost or stolen, is not the answer. PINs, passwords and signatures don't help either.
It's no surprise that for data industry leaders, when addressing the questions of physical access control, the overwhelming answer has been biometric technology, which provides a level of security beyond that of conventional card systems by verifying the identity of the person.
At the same time, they eliminate the burden and expense of a card-based system. Cards generally cost several dollars each, and reissuing them takes time. In addition, forgotten and misplaced cards diminish the effectiveness of a security system. Today, Internet data, telecommunications and co-location facilities around the world are using biometrics for their physical access control because they offer high security and convenience.
How Does It Work?
A hand geometry reader simultaneously analyzes more than 31,000 points and instantaneously records more than 90 separate measurements of a person's hand, including length, width, thickness and surface area, to verify the person's identification. In conjunction with a PIN or a swipe of a card, the registered person can gain access to the facility.
However, the authentication process involves a one-to-one search. A live biometric presented by the user is compared to a stored sample to confirm a match. The hand geometry or fingerprint of the user is not stored in a database or on an ID card. Instead, a mathematical equation, or algorithm, is performed with points measured on the finger or hand. The template that results from this equation is all that is stored.
When the user presents an ID card or enters a PIN, only that template is transmitted. When the employee presents his or her hand or finger, the reader runs the authentication process to determine if the template that is stored matches the biometric being presented. If there is a match, the person is authenticated.
Typically larger installations—such as Equinix, Level 3, Qwest Communications, XO Communications, Microsoft, Yahoo, Google, IBM, Bell South and Siemens— have used Schlage biometric hand readers at the entrance, in the security corridor and in the individual customer areas. Administration of the system is handled by HandNet for Windows software, which includes features tailored for this type of application, including import/export and remote enrollment for multifacility management and expiring privileges for temporary access. These hand readers interface to most access control panels and can be configured to control a lock independent of a panel.
The most common way to integrate biometrics is through card reader emulation. This method is especially effective when integrated into existing cardbased systems. The wiring is identical to the card reader's wiring.
In this mode, the biometric device essentially works with the access control panel in the same way a card reader does. The card reader output port of the biometric is connected to the panel's card reader port. When a person uses the biometric, it outputs the ID number of the individual if he or she is verified.
The format of the output is consistent with the card technology used by the access control panel. Once an ID number reaches the panel, it is handled as if it came from a card reader. The determination of granting access is made by the panel. The access control panel, not the biometric, handles door control and monitoring.
Working in the Data Center Industry
Internet data, telecommunications, interconnection and collocation facilities around the world are using Schlage biometrics for their physical access control.
The Equinix facilities are home to the world's largest content and enterprise companies such as AOL, Yahoo, Google, IBM, Sony and Paypal. To get a feel of the how the security systems come together, Equinix features a quick walk-through of their facility. At the front door, throughout the facility and at the independent cages, you will see hand readers at work, ensuring only authorized individuals gain entry.
Which Biometric Fits Your Application?
Hand and fingerprint readers make up 80 percent of biometric access control applications. They are complementary, as each meets specific needs in the market. When using these two technologies under a single platform, dealers, integrators and end users can create technology alternatives, fitting the appropriate biometric technology to each access point.
Fingerprint readers bring biometric security to low-volume applications. In fact, the low-cost technology is best used on doors accessed by fewer than 100 people. Such small-user populations are where most fingerprint readers are being used successfully.
In these applications, the total number of transactions tends to be fairly low. Therefore, issues generated by the higher error rates exhibited in fingerprint technology end up being a minor inconvenience rather than a major hassle. Yet, adding biometric technology provides a huge increase in security over a card-only system.
For these low-volume openings, cost is a key consideration and fingerprint products meet that need. For instance, a fingerprint reader is ideal for sensitive- document and high-value storage locations accessed by 10 to 30 people. This has been a major growth area for fingerprint products. They also can be incorporated into simple applications, like at the door to a medical cabinet.