
Cheating Wars in the Classroom
- By Scott N. Schober
- Jul 15, 2013
 Often, students think they are smarter than their teacher. Face it, the world has changed when it comes to technology. Hand any child a computer and they can intuitively figure things out faster than an adult. The same rule applies to mobile phones that are so commonplace that it is rare to find an individual without one.
Often, students think they are smarter than their teacher. Face it, the world has changed when it comes to technology. Hand any child a computer and they can intuitively figure things out faster than an adult. The same rule applies to mobile phones that are so commonplace that it is rare to find an individual without one.
Keeping in touch with our children when they are at school has gained importance in this uncertain world. The trouble arises when children misuse their mobile phones to get a better grade. From a young age, today’s children feel pressure to study hard to get into college to land a lucrative career. With the mounting pressure, many students resort to taking short cuts by taking the easy way out and cheating.
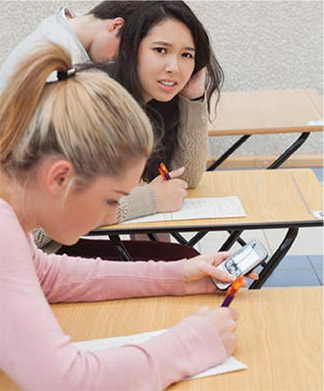
Cheating takes many forms: an innocent glance at the student’s exam in the adjacent row, or writing the answers on your palm. At the end of the day, cheating is wrong and should not be tolerated. Students turn to high-tech cheating with their mobile phones because they think their teachers aren’t savvy enough to catch them.
Students are tempted during exams to do a quick search on Google for the answer that slipped their mind. There also is a temptation to text their buddy across the room and ask for help on a question. You might wonder, “How can they text without getting caught?”
Many students are so proficient at texting that they only need to glance at the keyboard for a second. They hide their mobile phone under their desk, between their legs, or in their pockets, making it all the more challenging to catch. Plus, phones set on vibrate are virtually silent.
However, the vibration might give away their plan, so experienced cheaters resort to unique ring tones a teacher cannot hear. There are numerous ring tones that students download to their phones that will alert them to an incoming text or email. The interesting part is that people who are 20 years and older—like the teachers—cannot hear these “ultrasonic” tones. Reality is, they are not ultrasonic, but are in the hearing range that only younger ears can discern (typically 17 kHz and upwards). Teachers typically are more than 20 years old, and with time, hearing sensitivity degrades and the ability to hear higher frequency diminishes.
To help teachers take back control of the classroom, Berkeley Varitronics Systems has developed an affordable tool called the PocketHound cell phone detector. This device is small enough to fit in a teacher’s pocket so that they can covertly monitor for cheaters as they navigate between rows of desks during exams or while sitting at their desk. PocketHound will vibrate when there is a transmission from a mobile phone in close proximity, alerting the teacher to move in on the culprit. In addition, the bright blue LEDs provide a visual alert to the teacher as they approach the unsuspecting cheater.
PocketHound has an integrated, multiband antenna that is hidden under the label allowing for true stealth approaches. An internal rechargeable Li-ION battery has run-time of up to two hours. The product is simple to use with a single, integrated, jog slider control switch. The receiver continually scans all cell phone bands and uses a sophisticated algorithm that constantly samples the Radio Frequency (RF) noise floor to distinguish real cellular activity versus ambient RF noise.
This article originally appeared in the July 2013 issue of Security Today.
About the Author
Scott Schober is the president and CEO of Berkeley Varitronics Systems.