
High Profile Shootings Spur Rapid Growth of Market for US School Security System Integration
 In the wake of shooting tragedies including the Sandy Hook massacre, U.S. educational institutions are adopting systems that allow them to respond to all kinds of emergencies in real time, driving the country’s market for school security system integration to rise by more than 80 percent from 2012 to 2017.
In the wake of shooting tragedies including the Sandy Hook massacre, U.S. educational institutions are adopting systems that allow them to respond to all kinds of emergencies in real time, driving the country’s market for school security system integration to rise by more than 80 percent from 2012 to 2017.
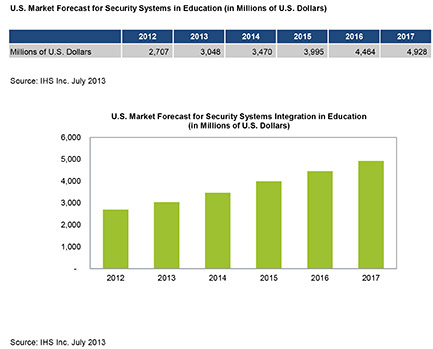
The market for security systems integration in educational institutions is set to expand to $4.9 billion in 2017, up from $2.7 billion in 2012, according to a new report entitled “Vertical Insights: Video Surveillance & Security in Education” from information and analytics provider IHS. Double-digit growth is expected for every year throughout the forecast, with revenue rising by 13 percent to reach $3.0 billion in 2013.
The system-integration business provides complete security solutions including the provision, installation and maintenance of video surveillance, physical access control and intruder alarm systems.
“Following events like Sandy Hook and the Santa Monica shooting, schools have changed their views of how security systems should work,” said Paul Bremner, video surveillance and security services market analyst at IHS. “Instead of serving as forensic tools that provide evidence of events that have already occurred, security systems now are expected to help educational institutions detect and mitigate problems as they happen. Because of this, schools are employing security system-integration providers, which provide technologies and services that combine multiple safety mechanisms into a cohesive solution.”
Video surveillance and security systems that can reduce the possibility, or that provide quicker response times to incidents as they are occurring, have an advantage over those that cannot.
“Video surveillance and security systems in the education sector must be flexible enough to deal with multiple types of threats,” Bremner said. “The types of threats an educational institution may encounter change during the course of a day. During the daytime, the main issue is access control, restricting who comes onto the premise and ensuring any potential threats remain outside. At night, the security system must deal with protection against vandalism.”
School security solutions in the past have centered on a combination of physical access control and emergency notification systems. While this approach is still a strong focus for many schools, there now is much higher demand for video surveillance equipment in educational institutions. The growth rate of the video surveillance equipment market in the education sector is more than double that of the equipment market for physical access control.
“In addition to dealing with threats, video surveillance systems in the education sector have the added advantage that they can be used for a broad range of tasks, including gathering evidence for a criminal investigation; acting as a deterrent for theft, assault and vandalism; or simply by providing greater visibility to the school’s security staff,” Bremner concluded.