Profitability Strains
RFID can address shrinking inventories
- By Michael Guiher
- Apr 01, 2017
A number of recommendations to address retail shrink came
out of the 2016 Retail Holiday Season Global Forecast, including
the following:
- Maintain operational execution standards, while being vigilant
regarding financial performance expectations.
- Update planning and financials to properly account for advanced
deliveries of seasonal products, since the seasonal build starts earlier
now than in the past. Enhance oversight to seasonal/holiday
merchandise to ensure financial goals are achieved while cost center
controls are contained.
- Properly train seasonal help to manage the increasing complexities
of the season.
- Employ technology to stabilize inventory loss and ensure on-shelf
availability while enhancing product protection countermeasures.
This last point is where RFID can play a critical role.
For most retailers, wholesalers and distributors, the space to
store inventory is the largest, yet single cost of doing business. From
purely a cost viewpoint, fewer inventories mean lower costs. At the
same time, unproductive or “dead” inventory as well as insufficient
inventory leads to out of stocks, lost sales and unhappy customers.
So balancing these two factors is critical to profitability and growth,
particularly in an omni-channel environment.
Additionally, retailers are increasingly leveraging RFID for its
loss prevention (LP) benefits. They are investigating RFID for numerous
reasons, including design considerations, store expansion
plans, understanding and addressing patterns of theft and increasing
the value of RFID inventory management initiatives.
Consider the following RFID LP applications.
Open Entrances
Mall stores often have open entrances, with merchandising close to
the exit door. For example, it is not uncommon to see mall stores and
luxury stores with open-entrance LP solutions seamlessly integrated
into the store design to enhance the shopping environment. RFIDbased
EAS provides format and usage flexibility.
Additional Insights and Analytics
Beyond informing retailers that a theft event may have occurred,
RFID can provide important information about quantity, value
and description of the inventory, enabling restocking to ensure shelf
availability and additional countermeasures to prevent future loss.
Consolidating Technologies
RFID-based EAS can serve as a “future proof” technology that can
accommodate new formats and information sharing down the road.
This lowers the incremental cost of RFID while expanding its benefits
to include LP.
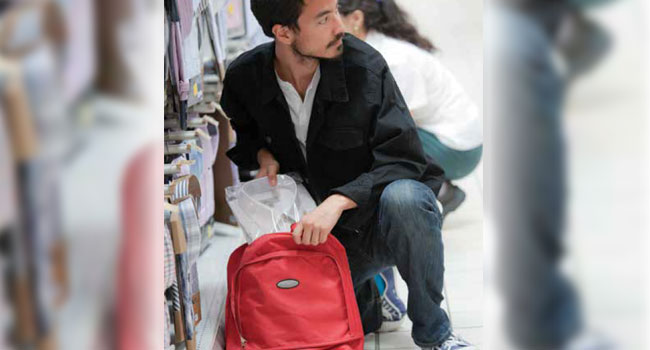
Organized Retail Crime
RFID is a new tool in the fight against ORC, providing differentiated
alarms for high volumes of merchandise and high-value items leaving
the exit door, as well as analysis to help prevent future incidents.
Inventory Management
When a retailer uses RFID for both inventory management and LP,
the same tags can be used for both, delivering significant cost savings
and labor savings for the organization.
For shoplifting and ORC, using RFID-based detection and prevention
can provide the following benefits:
- Item-level detail on what was stolen, enabling re-stocking to improve
on-shelf availability.
- Differentiated alarms – by quantity, value of items stolen.
- Protection for multiple merchandising formats including mall
stores and luxury stores.
- Automated, chain-wide alerts for ORC.
- Ability to analyze patterns of theft over time and respond.
Internal Theft
In addition to shoplifting, RFID is well suited to address internal
theft: It extends EAS to the dressing room, back room and other
“pre-POS” areas of the store. The technology can be used to improve
inventory visibility throughout the store. And it offers the ability to
analyze patterns of theft over time, enabling retailers
to respond accordingly.
Paired with effective training and operational
procedures, RFID is a proven piece of the overall
puzzle in fighting retail shrink.
This article originally appeared in the April 2017 issue of Security Today.
About the Author
Michael Guiher is the senior director of Global Product Management for Checkpoint Systems.