San Francisco Looking to Ban Facial Recognition Tech
A proposed ban in San Francisco has introduced a series of rules that could dramatically limit enhanced surveillance.
- By Sydny Shepard
- Feb 04, 2019
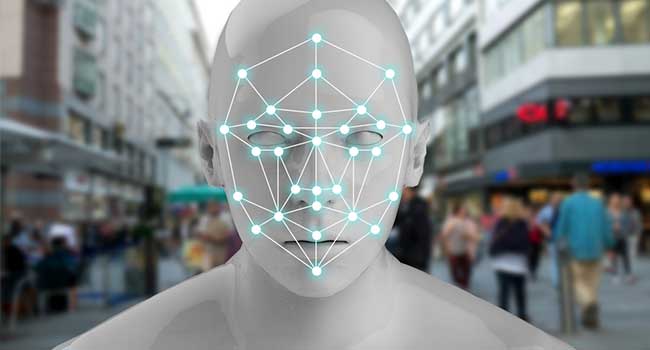
San Francisco could be the first U.S. city to ban its agencies from using facial recognition technology thanks to Aaron Peskin, a member of the city's Board of Supervisors, who has proposed a new suite of rules that could severely limit enhanced surveillance of the city.
The proposed ban was introduced last Tuesday and included a ban on facial recognition technology as well as strict rules on approval processes for new surveillance equipment bought by city agencies. The new ordnance would require agencies to gain the board's approval before buying new surveillance technology, putting the burden on city agencies to publicly explain why they want the tools as well as the potential harms.
The ordinance would also require an audit of any existing surveillance technology, including things like gunshot-detection systems, surveillance cameras, or automatic license plate readers. Officials would have to report annually on how the technology was used, community complaints and with whom they share the data.
The rules are similar to ordinances recently passed in nearby cities like Oakland and Santa Clara County, but San Francisco would be the first to official ban the use of facial recognition.
"I have yet to be persuaded that there is any beneficial use of this technology that outweighs the potential for government actors to use it for coercive and oppressive ends," Peskin said.
Critical like Peskin argue that, in the hands of the government, facial recognition enables all-too-easy access to real-time surveillance, especially given the availability of large databases of faces and names (driver's licenses, social media).
About the Author
Sydny Shepard is the Executive Editor of Campus Security & Life Safety.