Older Legacy Access Control Systems Leave Door Open to Cyberattacks
“Legacy access control systems use outdated technology that leaves them vulnerable to cyber threats, and can cause damage beyond the door,” cautions Thibault Louvet, director - Access Control Product Group at Genetec Inc.
With the average cost of a data breach being $3.9* million in damages, it’s never been more important for organizations to be educated on the risks associated with legacy systems and the advantages that a new cyber-secure access solution can offer.
Access Control Systems (ACS) are a powerful infrastructure tool that tend to be overlooked as a potential vector for cyber-attacks. In the past, they existed primarily to open and close doors but are increasingly used by businesses and government organizations to implement access rules, analyze building usage, and monitor for aberrant behavior and access requests within their facilities. As access control systems tend to be connected to an organization’s network, if a cybercriminal breaches a legacy ACS, not only can they open and close doors without permission, but they can also gain control over any other system that is connected to the network.
Once a network has been breached, all data becomes vulnerable, including sensitive information stored internally. Threat actors often look to move around a breached network to search for information that will generate the most financial gain. This usually leads them to valuable data like personal information about employees or customers, or an organization’s private financial data.
“Many organizations are holding on to access control systems that date back to more than 15 years,” says Louvet. “Although they are aware of the drawbacks of such a system, the thought of change is a daunting one for fear of costs, disruption of business, and the inability to take on more work. This results in them pouring more money and time into an old system that simply can’t keep up.”
Thankfully, the access control market is undergoing a huge transformation. Traditionally a proprietary market, it has now shifted to a more open one, providing customers with choices that better meet their unique needs. New, more cyber-secure solutions featuring end-to-end encryption and advanced authentication are now available, allowing end-users to do more with their system while protecting them from cyberattacks and malware.
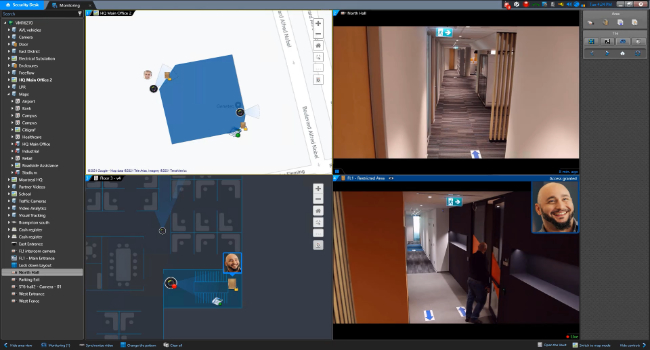
A unified access control system that uses the latest cybersecurity standards to secure communication, servers, and data such as Genetec Security Center Synergis™ can not only better protect an organization’s assets and people but help them improve their business operations and decision making that go beyond locking and unlocking doors. By choosing an open architecture IP-based access control system, organizations have the power to upgrade to the latest supported technology at any time, move at their own pace, and work within their available budget.
*Source: Report from IBM and the Ponemon Institute.