
Technology is providing small and medium-sized businesses (SMBs) of all industries a tremendous opportunity to grow and better manage their business.
- By Manny Johl
- May 09, 2019

People who belong to Generation Z may be overconfident about their online account security, suggests a recent survey commissioned by Google
- By Jessica Davis
- May 07, 2019

Find out how you should respond to being hacked.
- By Jerry Young
- May 06, 2019

The U.K. government is looking to step up IoT security against cybercriminals.
- By Sydny Shepard
- May 02, 2019

The inspector general believes D.C.'s transportation system is at a higher risk of cybersecurity attacks.
- By Sydny Shepard
- Apr 30, 2019

Some common areas and issues to keep growing your business, not your security risk.
- By Gary Brown
- Apr 26, 2019
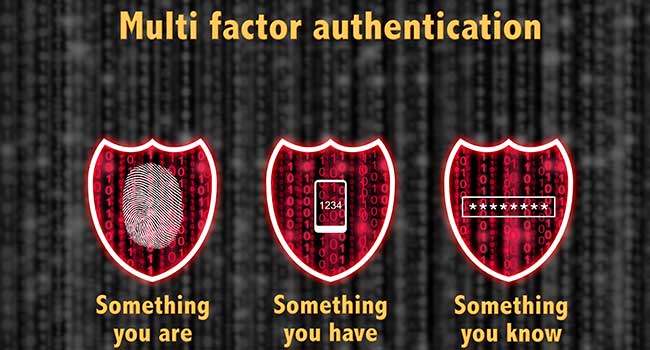
The U.S. Army is working toward adding more authentication measures to provide more options to access Army online resources while maintaining information technology system security.
- By Jessica Davis
- Apr 24, 2019

Hospitals are often in the news due to data breaches, and email hacks are often the cause.
- By Kayla Matthews
- Apr 19, 2019

Many companies are employing System and Organization Controls reports before procuring vendors' services.
- By Brad Thies
- Apr 18, 2019

What went wrong?
- By Kayla Matthews
- Apr 18, 2019

Six things you can do to be proactive against potential cyber crimes.
- By Kayla Matthews
- Apr 17, 2019

Are voice-enabled devices making you more vulnerable to cyberattack?
- By Sydny Shepard
- Apr 16, 2019

No one really knows why airlines have become a target as of late but with the rate of attacks this high, something is definitely going on.
- By Matthew Walker-Jones
- Apr 08, 2019

Facebook is in trouble again.

Strong passwords, two-factor authentication and good cyber hygiene will keep your personal information protected while browsing popular social media accounts.
- By Susan Alexandra
- Apr 04, 2019

Toyota's servers in Japan have been hacked, leaving millions of pieces of data left vulnerable.
- By Sydny Shepard
- Apr 02, 2019
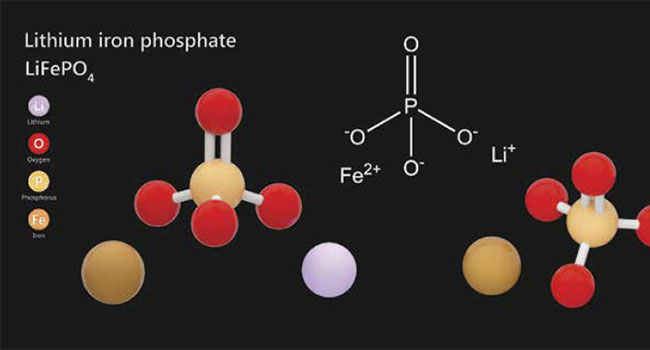
One of the primary criteria for any surveillance, access or security system is the requirement for a consistent and reliable power source, as even the most complex and expensive system solutions will be rendered useless if power is interrupted.
- By JR Andrews
- Apr 01, 2019

See no evil, hear no evil, speak no evil: It is tempting for physical security professionals to take this passive approach to cybersecurity.
- By Tom Galvin
- Apr 01, 2019

As cybercrime continues to plague companies of all sizes, across all industries both public and private, we wanted to take this opportunity to explore options that can help protect your data and your business.
- By Rich Aycock
- Apr 01, 2019

The breach exposed diagnostic results, healthcare numbers and personal contact information.
- By Sydny Shepard
- Mar 29, 2019