The security of corporate data is critical to the integrity of operations. Yet, everywhere we turn, it seems like another company has become victim to some form of cyber threat, malware or ransomware attack.
- By Francis Lachance
- Aug 01, 2017
It used to be that the most important aspect of implementing an electronic access control system was the simple control of who went where when. Today, the requirements of these sophisticated systems go beyond.
- By Scott Lindley
- Aug 01, 2017

Unreleased episodes of HBO shows and Game of Thrones scripts have been leaked as a result of the attack.

At the Annual Black Hat conference, Facebook Chief Security Officer Alex Stamos told the crowd that something needs to change in the security industry.

Prime Minister Stefan Lofven said the lead was a “disaster” and it exposed the nation to harm.

Televisions, fridges and other internet-connected home appliances should carry a security rating, a police chief suggested.

While flexibility is empowering the workforce, it is also complicating data security.
- By David Konetski
- Jul 20, 2017

Elon Musk commented on Tesla’s cybsersecurity during his talk at the National Governor’s Association this weekend.

Guests at 14 properties bearing the name of Trump might have their credit card information breached by hackers.

China has passed a cybersecurity law that requires foreign firms to store data within the country.
First Time Cases, Investigators Linked Globally

The government’s proposed cybersecurity legislation was necessary to take proactive measures to protect critical infrastructure.

The whole world could use a cybersecurity upgrade.
Common sense dictates that it is easier to stop something from happening in the first place than to repair the damage after it has been done.
- By Siva G. Narendra
- Jul 01, 2017
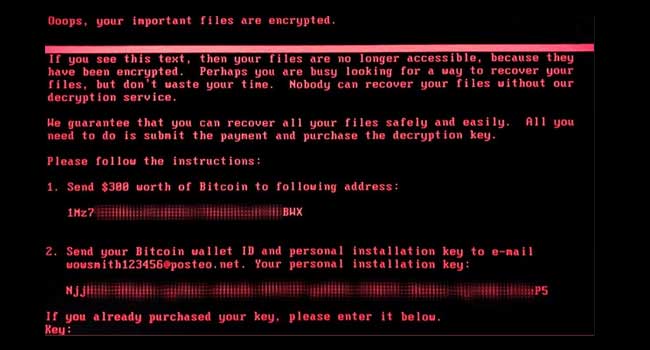
Yesterday, PC users across the world were asking for help as ransomware took data hostage and locked users out of their computers.

Government websites in Ohio, Maryland and New York were targeted.
Fewer than 90 email accounts with weak passwords are believed to have been hacked in “sustained” attack.

The education program is being developed in a partnership between the Girl Scouts and Palo Alto Networks.

For a relatively long time it seemed as if the password problem had been solved using SMS text messages.
- By Michael Lynch
- Jun 22, 2017

The cybersecurity arm of British intelligence services has reportedly suggested the global ransomware attack was launched from North Korea.