
A new report says some of the top baby monitors are vulnerable to basic hacking attempts.
- By Matt Holden
- Sep 02, 2015

From data breaches to security system compromises, there’s a ‘cloud’ hanging over hosted environments, labeling them unsafe or subject to easy compromise.
- By Brian Matthews, Ralph Shillington
- Sep 01, 2015

The ride service is significantly expanding its security team.
- By Matt Holden
- Aug 17, 2015

Security market to see rise of opportunities in cloud data center security.
- By Ginger Hill
- Aug 12, 2015

Since 2010 high-ranking officials' vacation plans, emails to friends and other correspondence has been targeted by China.
- By Ginger Hill
- Aug 11, 2015
New partnership helps ensure data integrity and operational continuity if a cyber-incident occurs.
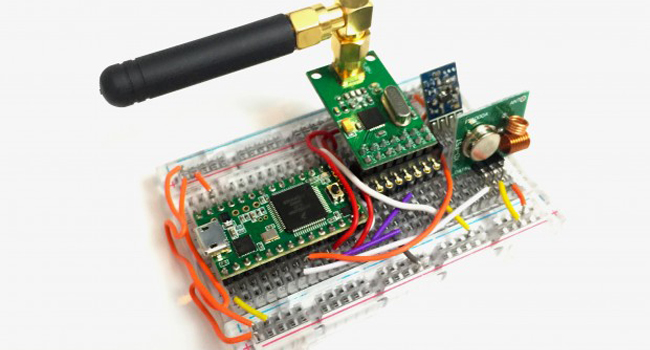
Small $30 device - Rolljam - enables entry into two of your most private places.
- By Ginger Hill
- Aug 10, 2015
Recent hacks expose personal information about millions of people.
- By Alison May
- Aug 06, 2015

Windows 10 features a number of security updates and settings that are important to know, even if you didn’t read the fine print.
- By Matt Holden
- Aug 05, 2015

Some public Wi-Fi hotspots are provided by con artists.
- By Matt Holden
- Aug 04, 2015

Intersecting business into the professionalization of information security debate.
- By Martin Zinaich
- Aug 04, 2015

The funding was led by TPG Growth.
- By Matt Holden
- Aug 03, 2015

5 steps to help professionalize the cybersecurity workforce.
- By Martin Zinaich
- Aug 03, 2015

Five key areas of understanding for information security directors.
- By Martin Zinaich
- Jul 31, 2015

Breaches of all sizes - small, medium and large - ruin reputations and can cost millions of dollars.
- By Martin Zinaich
- Jul 30, 2015

The devices can be hacked using a simple MMS message.
- By Matt Holden
- Jul 28, 2015

Mozilla also disabled the web-enabled video software.
- By Matt Holden
- Jul 15, 2015

Since introduction of computer passwords, not much has changed...until now.
- By Ginger Hill
- Jul 13, 2015

Credit monitoring and identity-theft protection offered to those affected.
- By Ginger Hill
- Jul 10, 2015

Take into consideration the hackers' motivation, then develop a plan of action.
- By Ginger Hill
- Jul 09, 2015