
There are many concerns when transferring to the cloud and security is one of the biggest, followed closely by concerns about complying with regulations and losing control of data according to a recent study by 451 Research.

A new study shows how mobile networks around the world have been hacked via bugs in the code.
- By Matt Holden
- Oct 15, 2015

After an attack on the App Store, iPhone and iPad users in China and Taiwan are still at risk.
- By Matt Holden
- Oct 05, 2015

A new report from Bluebox Security says the top 10 travel apps in the iOS and Android app stores are all riddled with security flaws. Bluebox says encryption app data, insufficient protection against man-in-the-middle attacks, and leftover administration or debugging code are the biggest issues for the iPhone and Android devices.
- By Matt Holden
- Sep 15, 2015

Every level of government developing ways to deal with physical security as well as the data their program produce.
- By Scott Cheatham
- Sep 14, 2015

You might not realize just how much you're actually sharing with complete strangers.
- By Ginger Hill
- Sep 11, 2015

The flaw could affect up to 200 million users.
- By Matt Holden
- Sep 09, 2015

A new report says some of the top baby monitors are vulnerable to basic hacking attempts.
- By Matt Holden
- Sep 02, 2015

From data breaches to security system compromises, there’s a ‘cloud’ hanging over hosted environments, labeling them unsafe or subject to easy compromise.
- By Brian Matthews, Ralph Shillington
- Sep 01, 2015

The ride service is significantly expanding its security team.
- By Matt Holden
- Aug 17, 2015

Security market to see rise of opportunities in cloud data center security.
- By Ginger Hill
- Aug 12, 2015

Since 2010 high-ranking officials' vacation plans, emails to friends and other correspondence has been targeted by China.
- By Ginger Hill
- Aug 11, 2015
New partnership helps ensure data integrity and operational continuity if a cyber-incident occurs.
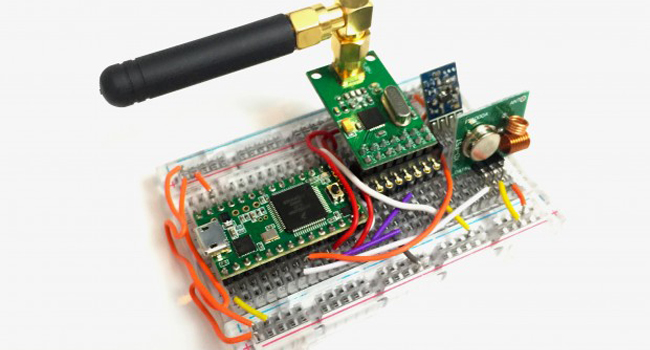
Small $30 device - Rolljam - enables entry into two of your most private places.
- By Ginger Hill
- Aug 10, 2015
Recent hacks expose personal information about millions of people.
- By Alison May
- Aug 06, 2015

Windows 10 features a number of security updates and settings that are important to know, even if you didn’t read the fine print.
- By Matt Holden
- Aug 05, 2015

Some public Wi-Fi hotspots are provided by con artists.
- By Matt Holden
- Aug 04, 2015

Intersecting business into the professionalization of information security debate.
- By Martin Zinaich
- Aug 04, 2015

The funding was led by TPG Growth.
- By Matt Holden
- Aug 03, 2015

5 steps to help professionalize the cybersecurity workforce.
- By Martin Zinaich
- Aug 03, 2015