KnowBe4 urges US institutions to take effective action to train employees before they fall victim to phishing attacks.

Executive actions aim to increase information sharing among private sector companies and federal law enforcement.
- By Matt Holden
- Feb 13, 2015

A line in the privacy policy states the television may record conversation and send it to a third party.
- By Matt Holden
- Feb 10, 2015

A report by U.S. Senator Edward Markey finds that most automakers don’t have the ability to find security breaches.
- By Matt Holden
- Feb 09, 2015

The President’s second, and final, national security strategy focuses on limiting how much the United States can shape world events.
- By Matt Holden
- Feb 06, 2015

The health insurance company is working with the FBI to come to a solution.
- By Matt Holden
- Feb 05, 2015

Paid out more than $1.5 million in 2014.
- By Ginger Hill
- Feb 03, 2015

The flaw could have potentially allowed hackers to open car doors.
- By Matt Holden
- Feb 02, 2015
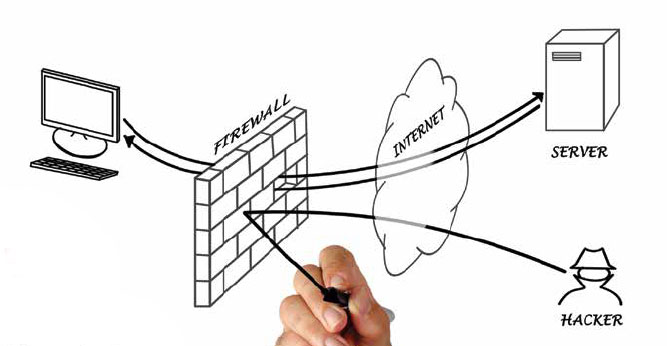
Money Movers Inc. is a fully PCI DSS compliant Electronic Funds Transfer Gateway processor. In plain English, that means we move a lot of data over a network.
- By Patrick E. Craig
- Feb 01, 2015

In a recent Hollywood comedy, Jason Segel’s character uttered the famous line, “Nobody understands the cloud. It’s a mystery.” And yet, all of us have been using the cloud for years: for online banking, online shopping, social media, email, sharing family photos and a host of other activities.
- By Jennifer Bruce
- Feb 01, 2015

The network-based physical security industry has matured rapidly over the past few years. As the technology and other components of security solutions have advanced, so too have the customer’s expectations.
- By Keven Marier
- Feb 01, 2015

Three strategies to keep you and your children safe from the prying eyes and ears of hackers.
- By Ginger Hill
- Jan 29, 2015
Scam sinks to new lows by targeting parents with fake “child predator in your area” emails.

One tech expert says biometrics are good, but there are still problems to consider.
- By Matt Holden
- Jan 29, 2015
National Data Privacy Day marked by new technology from TextPower, SnapID that verifies your identity while simplifying website logins and replaces usernames and passwords.
Executives are being targeted with phishing and ransomware to gain network access.

One commercial flight was diverted while two were also evacuated
- By Matt Holden
- Jan 27, 2015
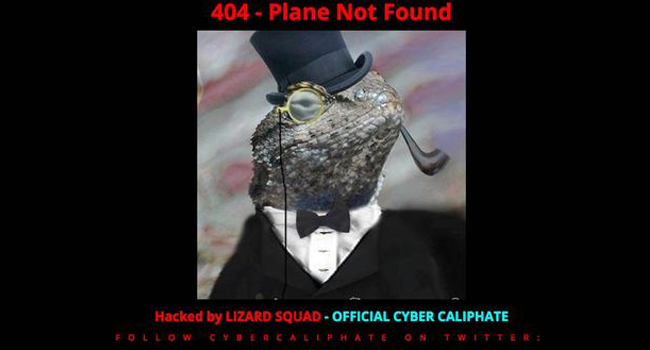
A case of domain hijacking determined by CyberSecurity Malaysia.
- By Ginger Hill
- Jan 26, 2015
First system able to process 2.5 billion transactions per day built for mobile economy; capable of real-time encryption for safest mobile transactions, capable of real-time analytics on transactions 17X faster than competition at a fraction of the cost.
Sera-Brynn discusses cyber security with Vice Pres. Biden and Secretary of Energy Moniz.