
The deputy director of the center is willing to look beyond his borders for cutting edge techniques
- By Matt Holden
- Dec 17, 2014
Solution designed as a cost-effective, high-storage efficiency appliance that secures vital company digital assets and deploys business-critical applications.

Advocacy group claims program is unconstitutional because it violates the 4th Amendment.
- By Ginger Hill
- Dec 17, 2014

These tips will help secure pay data when shopping online
- By Matt Holden
- Dec 16, 2014
Provide comprehensive cybersecurity information assurance, engineering and logistic support for Remote Visual Assessment (RVA) video surveillance system.
True self-replicating parasitic virus, VirRansom, demands 0.619 Bitcoin to let you back into your PC.

Government agency attempts to stand its ground against political leader.
- By Ginger Hill
- Dec 05, 2014

Social Security numbers appeared more than 1.1 million times in 601 publicly-posted files stolen by hackers.
- By Matt Holden
- Dec 05, 2014
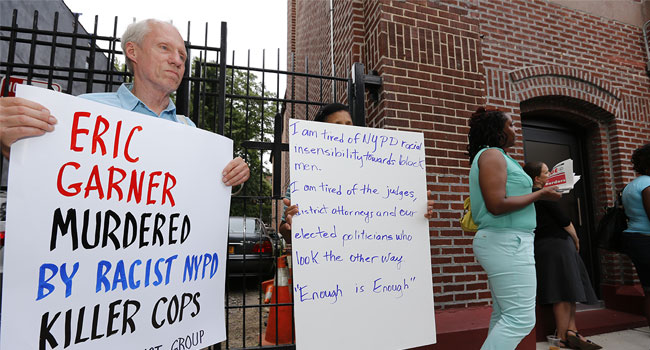
Critics attack NYPD after on social media after "wehearyou Tweet comes out soon after Eric Garner decision.
- By Ginger Hill
- Dec 04, 2014

A new report indicates consumers remain concerned about medical technology and the security of their health information and data.
- By Matt Holden
- Dec 04, 2014
Watch out for cybercriminals looking to make some extra cash during scam season - its a social engineering bonanza with threats on multiple fronts.

Business operations are coming back online after crippling attack.
- By Matt Holden
- Dec 02, 2014

FBI gains fresh intelligence and issues a security bulletin last night.
- By Ginger Hill
- Dec 01, 2014

The machine-to-machine (M2M) movement. The Internet of Things (IoT). The Internet of Everything (IoE). Each term may have its subtle differences, but at their core, they all involve connected devices that share information to enhance their intelligence, capabilities and operation.
- By Jeremy Brecher
- Dec 01, 2014

The survey was conducted by the Pew Research Center.
- By Matt Holden
- Nov 12, 2014

Luxury hotels have been the target of malware attacks.
- By Matt Holden
- Nov 10, 2014

The company also says the hackers got access via a vendor.
- By Matt Holden
- Nov 07, 2014

Wirelurker sneaks onto computers using unauthorized Chinese apps.
- By Ginger Hill
- Nov 06, 2014

IBM conducted a survey of nearly 150 security chiefs.
- By Matt Holden
- Nov 05, 2014

The European Network and Information Security Agency coordinated an exercise based in Athens.
- By Matt Holden
- Oct 31, 2014