
The airline will pay a maximum of one million miles to anyone who can prove a remote code execution.
- By Matt Holden
- May 15, 2015

Vehicles "talk" to each other to deliver location and speed information.
- By Ginger Hill
- May 14, 2015
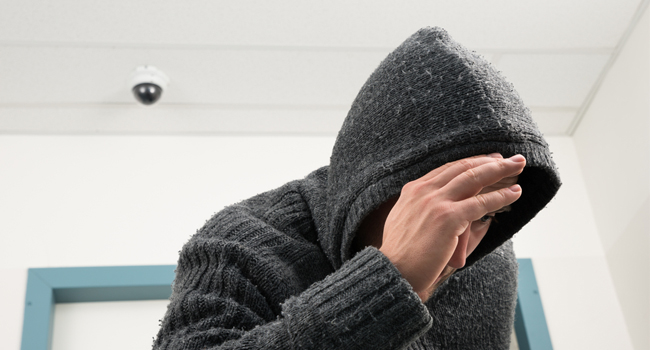
A woman was held hostage as three criminals stole her belongings.
- By Matt Holden
- May 14, 2015
Model organization tasked with implementing security integration throughout global enterprise.
To appear as witness at a House Homeland Security Committee hearing.
Offers durable and practical transparent solutions for any reader requirement.
Smart scene wizards, expanded test drive demo and dynamic new interface among improvements.
Nothing delivers the coverage, detection performance and cost-per-foot efficiency of New SightSensor XA.
Absolute Software report uncovers usage behavior and security risks of connected employees.
MyID technology allows customers to sign and encrypt email from mobile devices securely using WorxMail.
Security meets contemporary architectural design with Rockwood decorative pulls.
To offer better protection at an affordable price to most homeowners.

Likened app to a prisoner’s ankle bracelet, informing boss his actions are illegal.
- By Ginger Hill
- May 13, 2015

Users who have auto-reload setup on their digital card might be vulnerable.
- By Matt Holden
- May 13, 2015

Subway restaurants taking a stand against robbery and crime.
- By Ginger Hill
- May 12, 2015

Seemingly limitless system applications allows manufacturers to significantly increase capabilities of cameras and other devices.
- By Ronnie Pennington
- May 12, 2015

The league is beefing up security for the balls.
- By Matt Holden
- May 12, 2015
High-definition video as easy as 1-2-3.