All young security professionals at Security Industry Association (SIA) member companies and SIA student members may earn one of five $3,000 SIA RISE Scholarships.
ADT Commercial continues its strategic M&A strategy, expanding its nationwide geographic footprint and deepening its capabilities to serve mid-market, national and large-scale commercial customers in New York and New Jersey with today’s announcement it has purchased Deterrent Technologies, Inc., based out of Ocean, NJ.
The NFL Players Association is looking into a complaint filed by New York Jets players about the presence of security cameras in the locker room at their training facility in Florham Park, N.J., a source close to the union confirmed to ESPN.
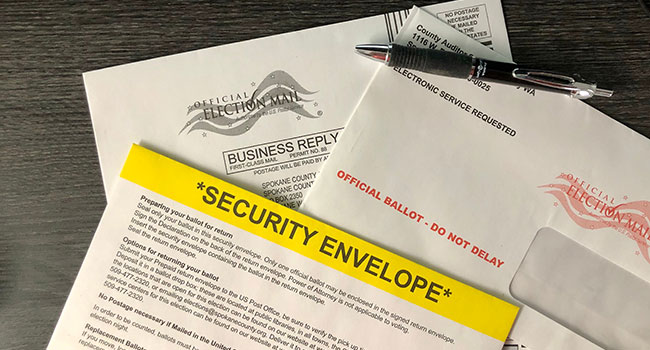
Here is a Q&A that answers questions about spoofing the voter. The answers come from Chris Krebbs, CISA director.
In an open letter to Twitter CEO Jack Dorsey, Department of Homeland Security (DHS) Acting Secretary Chad F. Wolf today called on Twitter to no longer obstruct Americans’ unalienable right to communicate with each other, their government, and its officials on the platform, because doing so endangers the national security.

The most recent elections is the most secure in the nation’s history. Or, is it? Government officials say it is the most secure ever.
ACRE has announced today the acquisition of Razberi Technologies based in Farmers Branch, Texas. This purchase will enhance ACRE’s strategic expansion plans for strengthening its video and communications business and product portfolio.
Houlton Station Border Patrol Agents and Border Patrol Explorer Post 1820 towed their Reconcraft 21’ RSDV boat down to Andy’s IGA in Houlton for the 2nd annual “Sink the Boat, Flood the Food Pantry” food drive on Oct. 31.
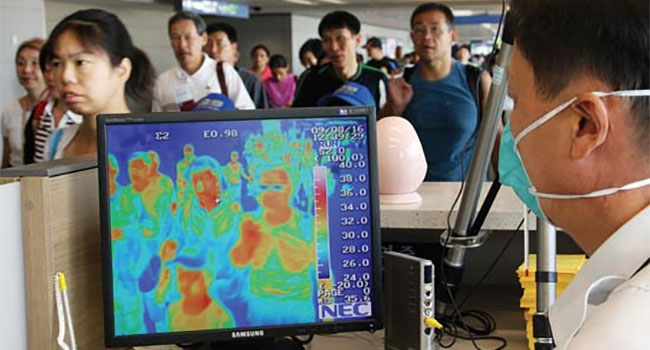
SIA recently submitted a letter to the Food and Drug Administration (FDA) Commissioner Stephen Hahn with a focus on an awareness that some companies are not following FDA guidelines related to the use of thermal imaging systems during the COVID-19 pandemic.

As we shop from the safety of our homes and fuel the digital economy, we expose ourselves to a great amount of risk, and fraudsters are taking advantage of this sharp increase in online shopping over the course of the COVID-19 crisis.
- By Thorsten Herbes
- Nov 02, 2020