Combination of technologies deliver unique solutions for IoT networking.
Electronic lock company has comprehensive suite of solutions for access control.
Simultaneous acquisitions of Protection 1 and ASG Security.

Critics have said the law might be used to eliminate dissent.
- By Matt Holden
- Jul 01, 2015

New Orleans is a terrific destination city. It is filled with history, music and adventure.
- By Ralph C. Jensen
- Jul 01, 2015
Any security investment starts with a realization that you have people and things to protect.
- By John Weadock
- Jul 01, 2015

Until recently, the Utah Transit Authority’s (UTA) video security system was limited by the capacities of its servers.
- By Courtney Pedersen
- Jul 01, 2015

At first glance, you’d think that sales representatives carry the heaviest burden for security dealers.
- By Robert Ogle
- Jul 01, 2015

Western Michigan University, located in Kalamazoo, Mich., is a national research university serving students from across the United States and 100 additional countries.
- By Taylor Foster
- Jul 01, 2015
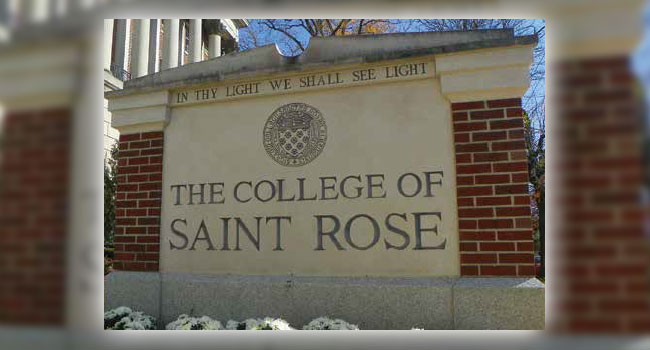
Located in the heart of Albany, N.Y.’s capital city, The College of Saint Rose offers 4,500 students a rigorous educational experience that extends their learning beyond the campus to the vibrant urban environment in which they live.
- By Mitchell Kane
- Jul 01, 2015