Extending Trust And Security
- By Bob Beliles
- Oct 19, 2009
Today, most organization officials understand they can use their IP network to connect physical security devices together. In some cases, the capital and operational cost savings from using a single communications infrastructure is enough to motivate them. But for others, further justification and additional benefits may be needed to drive convergence between the physical and the cyber worlds. And, most security and IT groups will also want to ensure the integrity of their respective systems and all data that may be shared between them.
The good news is there is a set of existing standards, created by the Trusted Computing Group (TCG), which has more than 100 members, which will secure both data and networked devices, as well as provide value by solving two common problems that virtually all organizations have:
- Do you know who followed your employees through the door today?
- Are your employees at their computers or have they left them unattended, exposing your network and other assets to a potential security breach?
A True Convergence
Most groups will acknowledge that these two common problems can lead to big headaches, such as theft of physical and logical (intellectual property, financial and customer data) assets, as well as corporate and/or regulatory compliance lapses. Unfortunately, most organizations have disparate policies and approaches to physical and cyber security, and with no employee incentive, organizations are simply hoping employees will police themselves and others.
Using TCG’s open Trusted Network Connect architecture and standards-based IF-MAP (which refers to Interface Metadata Access Protocol) suite can help solve these very real problems. Hirsch Electronics, Juniper Networks and Infoblox have teamed up to show how to close this gap in organizational security and to incentivize employees to follow applicable policies.
The result is a true convergence of physical access control security and network access control security where physical presence in a given location becomes a policy for granting or denying network access.
Here is how this works: an employee must “badge-in” at the door in order to get network access. Otherwise, the employee will be denied network access and will be required to make a trip back to a physical security credential reader before they will be granted network access. The same goes for exiting a building, if the employee requires network access via a Virtual Private Network connection, they must “badge out”.
In more technical terms, Hirsch’s Velocity PAC system uses IF-MAP to encrypt and transmit relevant access control event information (such as an authenticated user admitted to, or exited from, a building or particular zone) to a network-based clearinghouse for “metadata”. In turn, this clearinghouse uses IF-MAP to provide other trusted network devices, on a subscription-basis, with requested data about network events or, now, physical security events. These trusted devices then use this event data to make policy-based decisions as to what network resources a user can access based upon their physical location.
The whole concept is similar to social networking (like Twitter) for networked devices. Some devices “tweet” and other devices are listening for those “tweets.”
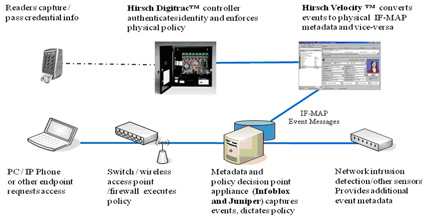
Figure 1: The Metadata Clearinghouse and Policy Decision-making Functions Can be Either Collapsed as Above or Discretely Implemented as Two Scalable Network Devices.
Trust-Based Architecture
By deploying this capability in their own physical and network security systems, organizations can safely share information between these two worlds and take comfort in knowing that these network devices are part of a trust-based architecture supported by leading IT and physical security companies. Furthermore, a wide range of additional policy-based network actions could be implemented in response to a physical or building system event.
For instance, since other building systems are interconnected to the access control system, such as the Hirsch Velocity server, those events can also be passed along to the network metadata clearinghouse supported by both Juniper and Infoblox. Such events can alert the network to a fire in the datacenter. In turn, the network, using the Juniper policy server, could respond by re-routing network traffic to a back-up datacenter.
The benefits for this type of convergence are multi-fold. At a minimum, by requiring employees to badge-in prior to gaining network access, organizations should see a significant reduction in “tailgating.” As a result, organizations will have more confidence in exactly who is inside their buildings at any given time; this is particularly important in the event of an emergency.
From a network security perspective, this solution adds yet another layer of protection to the network and its resources. Data theft and leakage from unattended PCs can be reduced. Fraudulent toll or fee-based charges from unauthorized IP phone usage can be decreased. And the illegitimate use of an employee’s username and password can be more easily detected and mitigated. For example, if the employee is in the building, but someone attempts to use his log-on information from somewhere else, the network will immediately recognize and respond to the policy violation with a network access denial, email notification, and even require a new password to be created.
And finally, organizations will not only have plugged a gap that has existed in their security policies, they will have the tool to better correlate physical and logical actions and flag possible “out of policy” events that can be an indicator of a compliance lapse. Thus, they will be able to demonstrate better control and policy enforcement during compliance audits including those for financial, corporate governance or healthcare/identity protection.
The Trusted Computing Group’s IF-MAP delivers on the real promise of network convergence. Not by simply sharing a network infrastructure, but by sharing information in new ways to enhance both physical and cyber security.
This open, standards-based protocol enables all adopting vendors to enable secure, trust-based communications among any sort of devices on the network. As a result, administrators can implement new policies which enhance both physical and network security and compliance, as well as track activity and set policies to monitor and quarantine such devices -- or take other action. Additionally, this capability helps to maximize every organization’s physical security and network infrastructure return on investment, which is particularly important in these challenging times.
About the Author
Bob Beliles is the senior manager for physical security market management at Cisco.