High-End Requirements
- By David Graas
- Oct 01, 2010
Video security in a digital world presents unique challenges as the industry transitions from historical analog to digital solutions.
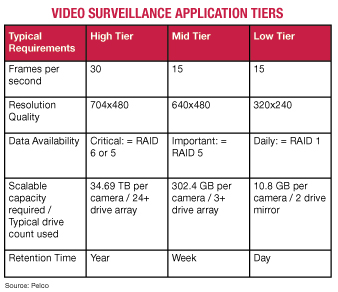
The shift to digital can impact business decisions, depending on your platform requirements. Higher levels of service, typically 24/7 full-motion security, demand higher levels of data availability, protection and performance. The other end of the curve is cost driven, where lower levels of service and features can be acceptable.
How do you satisfy both ends of the spectrum? Integrating a solid RAID solution, with plenty of cost/performance choices widely available, can meet the needs of these demanding storage system requirements.
Corporate or industry mandates, as well as local, state or federal compliance regulations, drive the need for higher service levels of video security.
Regardless of the reason, security staff that have relied on tapes are turning to information technology teams to develop more sophisticated surveillance applications that require high-powered digital security platforms.
System designs are no simple feat, especially for high-end applications that require full-motion, color, 24/7 operations with high levels of simultaneous writes to disk (recording) and reads (playback).
Enterprise storage systems, and the storage controllers integrated into them, are typically designed to meet the requirements of the applications they host. Most enterprise applications require faster read access -- e.g., database lookup and banking transactions -- than write access performance, yet approximately 95 percent of video surveillance I/O operations are write, or recording, intensive.
Data Availability, Protection
Security system providers often employ high levels of data protection and recovery to reduce the risk against data loss in mission-critical security areas -- airports, prisons and casinos. Maintaining data availability within these high tiers is strictly required to meet compliance regulations that are mandated to help protect people, places and equipment.
Video footage might be used as crucial evidence and referenced as critical discovery to support legal prosecution and investigation.
Think about the repercussions of a prison break and the risk that a prison system might incur if outdated equipment or security vulnerabilities were known by inmates. Or consider an airport security breach that could put hundreds of travelers in danger. Protecting this data is imperative -- which is why RAID is used in the design.
The storage system used for video data recording and playback also needs high levels of service availability, even when the disk array is rebuilding from a drive failure, which puts pressure on IT teams to include guaranteed minimum performance levels in non-optimal conditions to support camera feeds without interruption.
The Capacity and Retention Battle
With critical demands for video data retention increasing, the cost per gigabyte for deploying large storage footprints is now measured in petabytes.
For example, an application with 100 cameras can generate more than 30 terabytes of data weekly, and can require hundreds of simultaneous write and read operations for every camera.
These types of workloads can stress security systems hardware. Selecting the right RAID controller minimizes these potential problem areas.
The RAID level that is selected greatly depends on the final prioritization of the demands mentioned above. To derive the optimal storage solution, you need a strong understanding of the risks and the budget for the systems.
Generally, to support 24/7 operations, RAID 5 or 6 is the best choice, as it provides parity protection for up to two drive failures and allows administrators ample time to replace failed hard disk drives before data is compromised.
This also allows the system to keep running during the repair process. RAID 1 using two large-capacity drives can be used for low-cost systems and where video footage can be overwritten daily.
Selecting a Storage Solution
When migrating to a digital configuration, there are many variables to consider.
The number of hard drives used will dictate not only the capacity for storing video, but when used with a RAID controller, it also will support more camera streams and higher resolution.
The type of drive also is important, as a digital security system is considered a server environment, which means the drives should be designed specifically for that environment.
RAID controllers offer the benefit of protecting digital data and providing for real-time recovery for drive failures.
This helps minimize the maintenance requirements for 24/7 operations.
The cost factor can dictate the number of drives used for a system and what type of RAID is applicable. There also are multiple interface standards to choose from, such as SATA and SAS, as well as 3 GB and 6 GB generations of these technologies. The new 6 GB SAS technology has the advantage of supporting more throughput that can be needed when using the latest highresolution IP cameras. In the end, the design of the storage solution is driven by capacity, resolution, number of camera feeds and data availability needed by the end customer.
Many real-world benefits go along with a digital-based system. Because video is stored on hard drives rather than tapes, it allows for instant transfer of footage and support for backup and recovery similar to a server in a data center. Video also can be shared across standard networks, and frame-to-frame playback is easily done.
Simply put, the video data can be treated like any typical file on a computer for ease of use. While there can be additional costs for digital-based security capture, the overall benefits and increased quality will drive adoption of new storage platforms.
This article originally appeared in the issue of .