
Cultural Heritage Site Foils Thieves
- By Markus Breitbach
- Aug 02, 2013
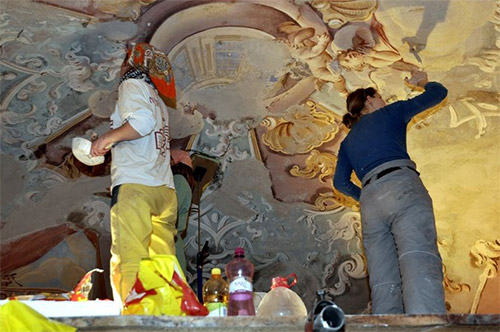 In the mid-18th century, Jesuit priests built three churches and 19 chapels east of the Slovakian mining town of Banská Štiavnica. The Baroque buildings – which house frescoes, sculptures and other works of art that depict Christ’s journey to the cross – once attracted pilgrims, but later fell into disrepair. When the Kalvársky Fund took note of the site’s cultural value and began restoring the buildings in 2008, metal thieves took notice, as well. Construction crews were making steady progress during the day, but at night, someone was sneaking up to Calvary Hill to snatch copper wire from the site’s power cables.
In the mid-18th century, Jesuit priests built three churches and 19 chapels east of the Slovakian mining town of Banská Štiavnica. The Baroque buildings – which house frescoes, sculptures and other works of art that depict Christ’s journey to the cross – once attracted pilgrims, but later fell into disrepair. When the Kalvársky Fund took note of the site’s cultural value and began restoring the buildings in 2008, metal thieves took notice, as well. Construction crews were making steady progress during the day, but at night, someone was sneaking up to Calvary Hill to snatch copper wire from the site’s power cables.
To solve the problem, the Kalvársky Fund went looking for an affordable mobile video surveillance system that could cover multiple locations and be controlled remotely. The solution came in the form of a video surveillance solution based on machine-to-machine (M2M) communication. The EyeSee, a surveillance solution from Deutsche Telekom partner Jablocom, fit the need.
The President of the fund, Martin Macharik, said that a mobile M2M camera has made the difference between restoring the Slovakian site and continuously delaying work to repair damaged power lines.
“Interruption of the power supply meant that we often had to call a halt to work for two or three days,” Macharik said. “But, we couldn’t monitor the entire Calvary since it is too large and unmanageable for that.”
Unfortunately, construction is not the only industry struggling with how to combat metal theft on sprawling, open properties, though. Railway companies and telecommunications groups are also seeking ways to protect their infrastructure from persistent criminals, intent on stealing valuable metal wiring.
The M2M benefit for security applications
 M2M is the automated interchange of information between several machines or between machines and a control center. In the security field, users adopt the technology not only to connect cameras wirelessly, but also to link alarm systems via the Internet and alert users when sensors indicate a fire, burglary or other problem. An M2M option saves users from the impossible task of continuously and manually evaluating camera images. Instead, the software in a mobile surveillance camera analyzes images and sensor data, contacting owners via a mobile network, if there is a security issue.
M2M is the automated interchange of information between several machines or between machines and a control center. In the security field, users adopt the technology not only to connect cameras wirelessly, but also to link alarm systems via the Internet and alert users when sensors indicate a fire, burglary or other problem. An M2M option saves users from the impossible task of continuously and manually evaluating camera images. Instead, the software in a mobile surveillance camera analyzes images and sensor data, contacting owners via a mobile network, if there is a security issue.
At the Calvary Hill site in Slovakia, the EyeSee surveillance camera uses a built-in, infrared, motion detector and senses human body temperature to recognize movements once the construction crews leave for the day. A motion in picture (MIP) detector regularly takes snapshots at the site, compares them and then records changes. If an intruder opens doors or windows, a sensor also picks up changes in atmospheric pressure, and an acoustic alarm can register the sound of breaking glass. A contact sensor prevents anyone from altering the camera’s position or angle, while an especially sensitive microphone registers sounds above a certain noise level. Data and alerts are relayed via mobile network.
Depending on their needs, users can set their profiles to prevent false alarms. In the open-air mode, for example, the camera scales down the sensitivity of its sensors, while in the business or house mode, the camera pays particular attention to movements of people, gusts of wind, significant changes in temperature or loud noises. The owner determines how stringent security needs to be by adjusting the reporting parameters and sensor sensitivity levels from an online portal.
This technology means that the Kalvársky Fund doesn’t need to rely on manpower to protect its valuable buildings, artwork or copper wires. If, for example, the M2M security camera notes a break-in based on the sensor data, it automatically calls the owner or sends a text message, multimedia message or e-mail. A fund employee gets a photo on his mobile phone that he can then share with the local authorities.
Since implementing the M2M security technology, the Kalvársky Fund has identified at least one thief, tightened the security of its site and progressed in its restoration without additional interruptions. The organization’s mobile surveillance technology will allow it to restore all of the site’s buildings and reopen them to the public. When pilgrims do return to view the Baroque buildings and the priceless art inside, up to eight mobile M2M surveillance cameras will keep watch and ensure the site’s ongoing security.
About the author:
 Markus Breitbach is vice president of global sales and marketing at Deutsche Telekom’s M2M Competence Center. He has more than 20 years of IT experience and is responsible for many activities within the Deutsche Telekom’s Global M2M unit, including the founding of the company’s M2M Marketplace, a global B2B e-Commerce platform that connects business customers with M2M suppliers.
Markus Breitbach is vice president of global sales and marketing at Deutsche Telekom’s M2M Competence Center. He has more than 20 years of IT experience and is responsible for many activities within the Deutsche Telekom’s Global M2M unit, including the founding of the company’s M2M Marketplace, a global B2B e-Commerce platform that connects business customers with M2M suppliers.