Quantum Secure Debuts SAFE for Secure Cloud
Quantum Secure announces the launch of SAFE for Secure Cloud, broadly increasing the accessibility of their premium physical identity and access management (PIAM) solution. As an alternative to on-premise deployment, SAFE for Secure Cloud leverages Quantum Secure’s sophisticated software which is presently in use at over 100 high profile private and public sites globally. The new cloud offering provides SMB users with a highly sophisticated and cost-effective PIAM solution that can increase security across multiple business operations, while providing resellers catering to the SMB market with new business development opportunities.
 “SAFE for Secure Cloud vastly extends our business model to include SMBs and the professional security resellers who service this tremendous market,” said Ajay Jain, president and CEO, Quantum Secure. “By deploying SAFE as a ready-to-use web-based solution, SMBs can dramatically increase physical and cyber security while reducing overall costs.”
“SAFE for Secure Cloud vastly extends our business model to include SMBs and the professional security resellers who service this tremendous market,” said Ajay Jain, president and CEO, Quantum Secure. “By deploying SAFE as a ready-to-use web-based solution, SMBs can dramatically increase physical and cyber security while reducing overall costs.”
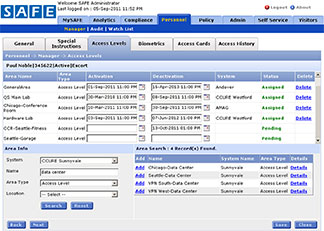
SAFE for Secure Cloud solves complex PIAM challenges for SMBs including the ability to: on-board and off-board personnel; establish and implement role-based physical access assignments across single or multiple systems; support regulatory governance and compliance; conduct audits and generate reports. In addition, SAFE for Secure Cloud securely integrates with human resources, contractor management, training, and physical access control systems. Small and mid-sized companies can be up and running with SAFE for Secure Cloud rapidly without the added costs associated with specialized personnel and system administrators, and dedicated software and servers. In addition to providing a new solution for SMBs to improve physical and cyber security, SAFE for Secure Cloud ultimately lowers costs.
SAFE for Secure Cloud provides professional security resellers with new business opportunities in the SMB market by providing an exclusive and proprietary solution offering that can generate a new stream of recurring monthly revenues.