Hackers Working at Top Speed to Gain Entry into Your Car and Home
- By Ginger Hill
- Aug 10, 2015
We live in a world that is always moving at top speed. When I ask someone how they’re doing, 9 times out of 10, I’ll get, “Busy, so busy!” as the answer. The same is true when it comes to security and hacking, too. It seems like hackers devise 10 new tools by the time the security industry comes up with one effective way to block an old hack! So, are we every really safe? Here’s yet another device that reveals just how vulnerable we really are.
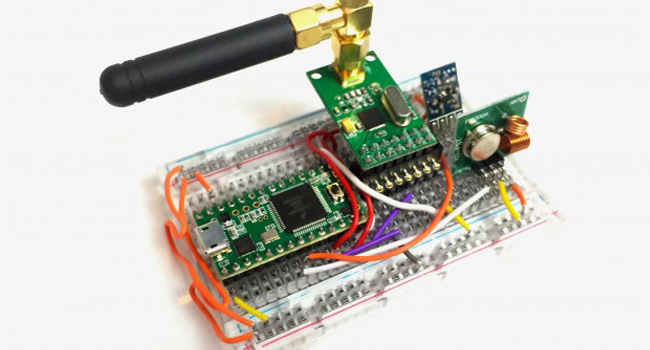
Introducing “Rolljam,” a tiny device that is very simple to use, yet devious and brilliant all at the same time, and it’s used to break into just about any vehicle or home. The device is composed of a tiny series of circuit boards with three build-in radios. Two of the radios are used to jam the wireless signals sent out by a car’s keyless remote entry and the third radio reads the transmitted code, storing it on the device.
Keyless entry on cars usually use rolling codes so that once a certain code is used, it can’t be used again. Here lies the brilliance of Rolljam. Because it blocks the signal while being transmitted from a car’s key fob, the code never reaches its intended destination. When the owner presses the unlock button again, a new code is transmitted that successfully unlocks the car. Therefore, the first code was never used, so Rolljam transmits it later to successfully unlock the car.
So far, Rolljam has worked on Nissan, Cadillac, Ford, Toyota, Lotus, Volkswagen and Chrysler brands along with various brands of garage door openers.
And, here’s the big kicker: Rolljam only costs $30!
(Image from http://paultan.org/2015/08/10/all-it-takes-is-rm120-to-unlock-cars-with-rolljam/)
About the Author
Ginger Hill is Group Social Media Manager.