People are fallible creatures. As the saying goes, nobody’s perfect.
- By Jason Cronk
- Sep 01, 2018

Healthcare institutions face a variety of cybersecurity challenges, and the threats continue to grow and evolve. Hospitals are particularly vulnerable to data breaches and ransomware attacks because of the high value of healthcare data
- By Sheila Loy
- Sep 01, 2018

Google Chrome is largely considered one of the most security-conscious browsers, but recent headlines revealed some of its weaknesses.
- By David Pearson
- Sep 01, 2018

Drones can provide significant benefits for residents and business in rural areas: delivering medical supplies, collecting data on the status of crops, aiding in search and rescue efforts.
- By Matthew Leonard
- Sep 01, 2018

With the high availability of today’s mobile network coverage and accessibility to public Wi-Fi hotspots, secure connectivity is often overlooked by traveling professionals.
- By Julian Weinberger
- Sep 01, 2018
Wi-Fi is a technology based on the IEEE 802.11 suite of standards that uses radio frequencies (RF) extend wired Ethernet-based local area networks (LAN) to Wi-Fi-enabled devices, allowing the devices to receive and send information from the internet.
- By Andrew Jimenez
- Sep 01, 2018

We all are talking to machines these days. We talk to assistants in our home, in our cars and on our phones. By using our voice, we feel more engaged. We also become more productive, freeing our hands and minds for other tasks.
- By Jim Hoffpauir
- Sep 01, 2018

About two million people are affected by workplace violence every year in the United States. Some of these people are parking enforcement officers.
- By Chris Yigit
- Sep 01, 2018

The surveillance technology initially installed at the site was triggered by outdoor motion sensors that activated any one of several PTZ cameras for verification—unfortunately this set-up generated far too many false alarms to be effective.
- By Suzi Abell
- Sep 01, 2018

Cloud technology began with the concept of grid computing— the idea that we could replicate the way a power grid in a country was set up.
- By Peter Boriskin
- Sep 01, 2018

Technology innovations are being introduced to the market at an increasingly accelerated pace and the established multi-national companies that have long enjoyed strong market shares and growth rates are being challenged by hundreds of startups.
- By Robert Lydic
- Sep 01, 2018
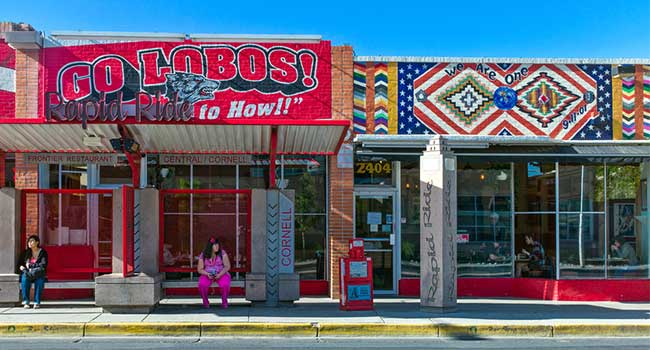
New Program puts 88 more cameras on Albuquerque’s streets.
- By Jordan Lutke
- Aug 31, 2018

A man defied security measures to kill his bedridden wife and himself, rattling hospital staff.
- By Jordan Lutke
- Aug 31, 2018

A man faces a criminal charge after police say he threatened to commit a mass shooting at a school using a 3D-printed gun.

The new tools will make it easier for users to protect their accounts.
- By Sydny Shepard
- Aug 30, 2018

The fall out from the Jacksonville shooting includes lawsuits, event cancellations and increased security for future gaming conventions.
- By Sydny Shepard
- Aug 29, 2018

The importance of communication in preventing and remediating cyberattacks
- By Vincent Geffray
- Aug 28, 2018

The esports industry calls for increased security following the death of two esports players at a tournament.
- By Sydny Shepard
- Aug 28, 2018

Last week was not a good week for telecommunications companies.
- By Sydny Shepard
- Aug 28, 2018
Netwatch Group appoints Mike Taylor as VP of US Sales, unifying the US presence and introducing a single sales organization.

Two people were killed and several others were injured by a gunman at a Madden 19 tournament in Jacksonville, Fla.
- By Sydny Shepard
- Aug 27, 2018

Armed guards and metal detectors are chief among the new measures being taken to ensure the safety of patients.
- By Jordan Lutke
- Aug 24, 2018

Police were able to track down a suspect after receiving security camera footage from a home near the site where Mollie Tibbetts disappeared.
- By Sydny Shepard
- Aug 23, 2018

Even if guests put up a “Do Not Disturb” sign on their door, security will enter the room to perform the search.
- By Jordan Lutke
- Aug 23, 2018

The threats of cyberattacks are increasing, spurring the recent invention and patenting of technologies like freeze logic.
- By Jordan Lutke
- Aug 22, 2018

The city is looking into adding plexiglass dividers between drivers and riders to cut down on assaults.
- By Sydny Shepard
- Aug 21, 2018