
A line in the privacy policy states the television may record conversation and send it to a third party.
- By Matt Holden
- Feb 10, 2015
Canon Inc. has announced a public offer to the shareholders of Axis to transfer all of their shares in Axis to Canon. The total value of the offer is SEK 23.6 billion

A report by U.S. Senator Edward Markey finds that most automakers don’t have the ability to find security breaches.
- By Matt Holden
- Feb 09, 2015

SAFFiR and his drone sidekick, Damage Control Technologies, help keep sailors out of direct exposure to fire.
- By Ginger Hill
- Feb 06, 2015

The President’s second, and final, national security strategy focuses on limiting how much the United States can shape world events.
- By Matt Holden
- Feb 06, 2015
Company representatives to share information on latest in video surveillance and products.
Several technologies are available that help detect misuse of taxpayer information.
- By Hagai Schaffer
- Feb 05, 2015

Filming action movies on Paris streets banned in response to recent terrorist attacks.
- By Ginger Hill
- Feb 05, 2015

The health insurance company is working with the FBI to come to a solution.
- By Matt Holden
- Feb 05, 2015
Enables long range Ethernet over Coax or CAT5e and supports Hi-PoE and PoE/PoE+ at longer distances.
First result of a strategic collaboration with Milestone on video-enabled experience in parks.
Video surveillance isn't a luxury; it's a necessity.
Company continues commitment to furthering loss prevention education.
ESA-certified DW Spectrum IP VMS classes available for 2015.
Smart Payment Association announces preliminary finds of 2014 smart card payments review.

By 2019, it is predicted that more than half a billion wearable devices will be in use each day.
- By Ginger Hill
- Feb 04, 2015

Officials have admitted that it is a gap in security.
- By Matt Holden
- Feb 04, 2015

Paid out more than $1.5 million in 2014.
- By Ginger Hill
- Feb 03, 2015
Goal is to strengthen North American education market.
Complementary add-on and extension for dealers transition into the smart home market.
Seamlessly translates between English, Spanish and French.
Growing need for accurate, reliable and mobile LPR to combat speeding in areas with no fixed monitoring.

The bomb in Alexandria front of the Mabaret Al-Asafra Hospital killed a 27-year-old man and wounded three others.
- By Matt Holden
- Feb 03, 2015
1 Day Only - March 5 in Palmdale, Calif.
New Linux Cube LX will replace Blackjack Blade as advanced, Linux-based, small venue, IP recording solution.

University of Virginia fraternities allowed to carry on as usual while sororities weren't allowed to participate.
- By Ginger Hill
- Feb 02, 2015
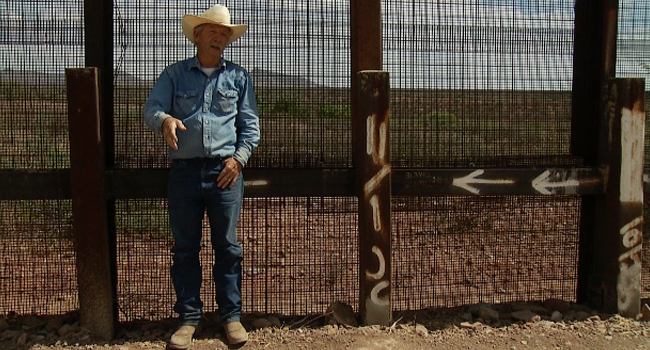
Fencing between Arizona and Mexico could cause some species' population to decrease or become extinct.
- By Ginger Hill
- Feb 02, 2015
Long-trusted detection technologies increasingly ineffective says 75% of IT and security professionals in findings released by Spikes Security and Ponemon Institute.
City of Guayaquil leverages integrated surveillance platform to share intelligence across agencies, expedite investigations and mitigate crime.
DVR offers unparalleled image quality at an affordable cost.