
The predicted increase in online fraud in the U.S. has arrived with the adoption of chip card technology.
- By Michael Lynch
- Mar 16, 2017

Four people, including two officers from Russian security services, were charged by the U.S. in the massive data breach that plagued Yahoo.
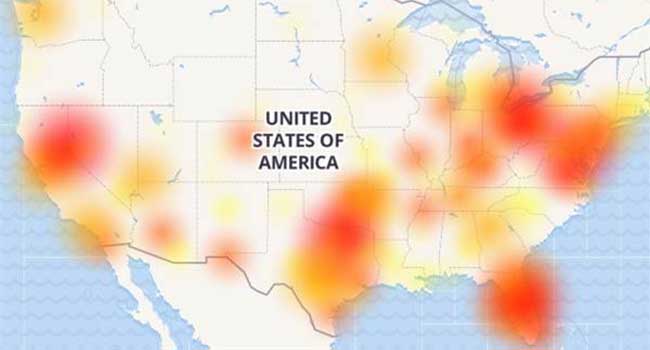
Users of AT&T’s wireless network found themselves without the ability to call 911 last night.

Today as the cybersecurity landscape continues to evolve at breakneck speed, so do the threats, and the amount of data we have sitting with the different organizations we deal with is growing each day.
- By Brett Hansen
- Mar 09, 2017

WikiLeaks released thousands of documents that it said described hacking methods of the CIA.

Milestone Systems is the number one VMS worldwide, but they are searching for more.

Software bug at an internet-service provider sparks privacy and security concerns.

Local, federal, state and private security officials are teaming up to create a security stronghold that protects a three mile area around the stadium.

Earlier in 2016, when Gartner analysts stated that by 2020, 80 percent of all software will be offered on a subscription basis—this did not come as surprise to us at Genetec.
- By Christian Morin
- Feb 01, 2017
Financial institutions have been historically slow to adopt IP video surveillance citing concerns about possibly compromising network security.
- By Stephen Joseph
- Feb 01, 2017
Security threats are on the rise and as IT security teams increase their scrutiny of all network-connected devices, it’s time for some new thinking about the design and maintenance of building security systems.
- By John Szczygiel
- Feb 01, 2017

A hacker just wants President Trump to change his security settings on Twitter.

Washington D.C. Police along with Secret Service and the FBI have been working to secure the Presidential Inauguration for over a year.
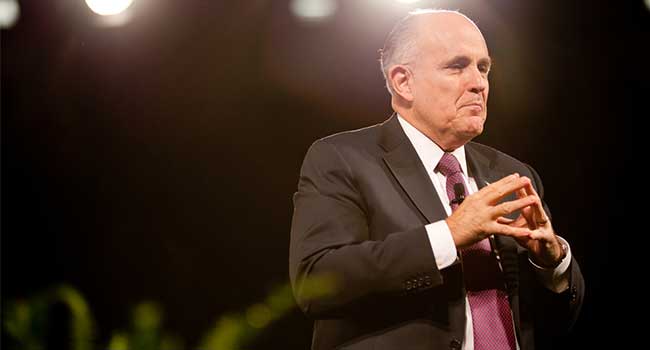
President-Elect chooses Rudy Giuliani to hold private industry meetings on cybersecurity.

Maybe it’s time for a different (and maybe more affordably efficient) approach.
- By Mike McCamon
- Jan 11, 2017

While these topics may seem somewhat disparate, there is actually a common thread among them: They all have security officers and end users concerned.
- By Dean Wiech
- Jan 06, 2017

Security firm LogRhythm has predicted the internet will shut down for 24 hours in 2017 due to a massive DDoS attack.

The annual Consumer Electronics Show had many security companies showing off their latest innovations.

Resolutions to keep your 2017 free of the most common security blunders.

Vehicle attacks, hacks and police ambushes make the list of top physical security events of 2016.