
More than four in five U.S. physicians (83 percent) have experienced some form of cyberattack, according to new survey research released by Accenture and the American Medical Association.
- By Jessica Davis
- Dec 14, 2017

Experian’s Data Breach Resolution released its Data Breach Industry Forecast on Tuesday in an effort to help key business decision makers prepare against cybercrime in the year ahead.
- By Jessica Davis
- Dec 13, 2017

An upcoming ruling by the Supreme Court of the United States (SCOTUS) may drastically change how and where CSPs decide to store customer data.
- By Brad Thies
- Dec 11, 2017

Mecklenburg County, N.C., is working toward fixing its computer systems after refusing to pay a hacker who used ransomware to freeze dozens of local government servers.
- By Jessica Davis
- Dec 08, 2017

The bill comes in the wake of news that Uber handled a breach affecting as many as 57 million consumers by paying the hackers $100,000 in exchange for their silence.
- By Jessica Davis
- Dec 05, 2017

Despite the answers a bit of saliva can provide, some are critical of the at-home test services, questioning the level of security they provide for your most sensitive information.
- By Jessica Davis
- Dec 05, 2017
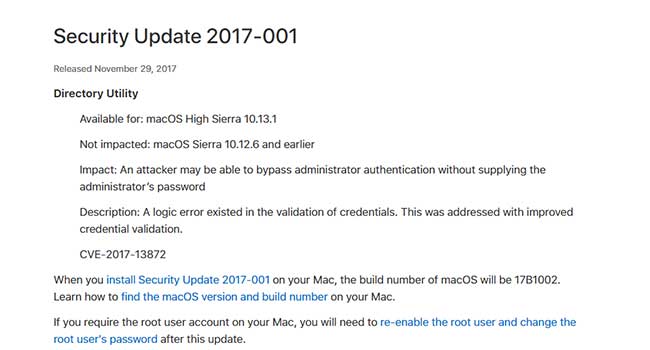
Apple has patched a macOS High Sierra flaw that would allow intruders to gain full administrator access on your system.
- By Jessica Davis
- Nov 30, 2017
Being online puts you and your data at risk, but there are ways you can minimize your risk and make a hacker’s job harder.
- By Jessica Davis
- Nov 29, 2017

With hacks, attacks, ransoms and even extortion attempts, 2017 has been the year of data breaches, and it’s not even over yet.
- By Ankur Laroia
- Nov 24, 2017

Kaspersky Lab’s review of phishing attacks during the holiday sales season found that the number of phishing attacks can decrease by as much as 33 percent on the day after Black Friday.
- By Jessica Davis
- Nov 20, 2017

Amazon has addressed the hack and will be rolling out an update next week.
- By Sydny Shepard
- Nov 17, 2017

The goal of the new security module, Google said, is to prevent attackers from decrypting your data without knowing your password by reinforcing the lock screen against attacks.
- By Jessica Davis
- Nov 16, 2017

Days after the iPhone X’s official release, hackers in Vietnam have successfully tricked Face ID and unlocked the smartphone with a 3-D-printed mask.
- By Jessica Davis
- Nov 15, 2017

The survey was based on responses from 603 IT and line-of-business decision-makers involved in enterprise security teams across the US, UK, Germany, France, Australia and New Zealand.
- By Jessica Davis
- Nov 13, 2017

iOS 11 has some settings you should adjust to keep a tighter lid on your online privacy and security.
- By Jessica Davis
- Nov 08, 2017

The temporary deactivation Thursday of the personal Twitter account of President Donald Trump, @realDonaldTrump, by a customer support employee on their last day of employment has raised questions about Twitter’s internal security.
- By Jessica Davis
- Nov 06, 2017

The iPhone X releases today, and with it come more concerns about the privacy and security of its new Face ID feature.
- By Jessica Davis
- Nov 03, 2017

This year has been filled with some of the biggest data breaches in history, which is a truly horrific thought.
- By Tyler Reguly
- Oct 31, 2017

How researching and investing in these three technologies will change your business
- By Todd Kleperis
- Oct 30, 2017

Without these online tools, your business could be vulnerable to cyberattacks risking the information of your employees and customers.
- By Sydny Shepard
- Oct 27, 2017