
Once upon a time, this was the year when cars could fly, human immune systems healed themselves and cops could stop a crime dead in its tracks. While some of these things are still more of a dream than a reality, the last one is becoming more viable every day.
- By Clayton Brown
- Dec 01, 2019

Large employers like Google, Facebook, Johnson & Johnson and Apple have committed to closing the gap of cybersecurity jobs.
- By Haley Samsel
- Oct 31, 2019
In today’s IP-centric world, media converters work on lots of different types of media. The three that this article discusses are fiber optic media converters, extended distance media converters, and wireless media converters, all of which are transmitting an Ethernet signal
- By Frank (Skip) Haight
- Oct 01, 2019

In today’s world, there are a myriad of different manufacturers that produce similar products and there are so many options available to customers.
- By Michael Stoll
- Oct 01, 2019
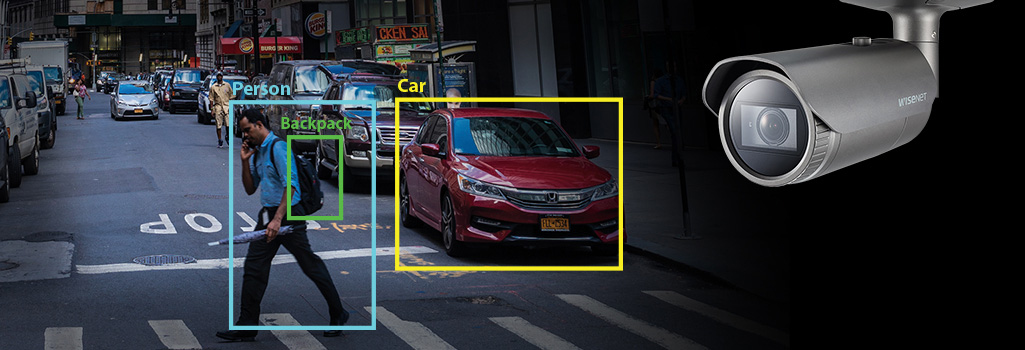
Today, there are in-depth discussions about what ‘might be’ possible with AI, machine and deep learning-based analytics products on the market.

The peace of mind that comes with the IDIS Total Solution begins in Seoul, Korea. IDIS’s ground-breaking DirectIP™ technology is at the heart of the IDIS Total Solution for video surveillance.

The number and breadth of devices that make up the Internet of Things (IoT) continues to grow rapidly, with everything from kitchen appliances to video surveillance and access control systems offering the ability to connect to a network.
- By Ryan Zatolokin
- Sep 01, 2019

We know by now that there is an abundance of business advantages in the cloud — it’s agile and cost-efficient, and, with little to no hardware maintenance, it’s easier to update and perform maintenance on than traditional on-site servers.

A new IT trend–“hyperconvergence”–may hold the key to simplifying this task while also enabling significantly more sophisticated ways to tap the value of data many organizations are already collecting.
- By Eric Bassier
- Sep 01, 2019
The world of outdoor security cameras is changing rapidly, and with it, the need for secure, high-quality camera housing.
- By Kaitlyn DeHaven
- Sep 01, 2019

Today’s property manager has many tasks to complete on a daily basis: navigating the ins and outs of the business, ensuring that all processes, systems and personnel are in place to secure their physical assets, and creating a positive environment for tenants and visitors.
- By Greg Falahee
- Sep 01, 2019

Providing security, managing budgets, gaining efficiencies— these are just a few of the many objectives that facility managers have to balance at once.
- By Jeremy Saline
- Sep 01, 2019

Safe cities attract businesses, foster innovation and provide countless opportunities. By working collaboratively, both public and private sectors can contribute to a solid foundation for the success of these great cities and their citizens.
- By Bob Carter
- Sep 01, 2019

Do you want the real bottom line in providing cloud services for video, access control and other integrated services?
- By Martin Renkis
- Sep 01, 2019

Security professionals face many challenges in selecting video surveillance systems that address their unique needs.
- By Jeff Whitney
- Sep 01, 2019

How to rebut the common (and illegitimate) excuses used by third-parties for not complying with your information security due diligence requests
- By Evan Francen
- Aug 02, 2019
While video surveillance often takes center stage in security deployments, equally as important is audio.
- By Richard Brent
- Aug 01, 2019
Although IP-based network cameras are the prevailing standard for new installations, it wasn’t that long ago that analog cameras, and the complex infrastructures required to support large numbers of them, were the only way to accomplish the job.
- By Robert Wegner
- Jun 01, 2019
At the start of every new year, I get a sampling of what new technologies are going to be introduced. Most of the time, I’m in way over my head. Sometimes I understand and relate to the solution, the technology and what it all means.

When this upgrade project began in early 2017, there was a mix of standard-resolution legacy video cameras scattered throughout the facilities.
- By Courtney Dillon Pedersen
- Jun 01, 2019