
A security flaw in Facebook’s Messenger platform allowed hackers to edit conversation and implant malicious links.
- By Sydny Shepard
- Jun 07, 2016

By definition, PIAM is an end-to-end solution that manages identities, compliance and events across disparate physical security systems.
- By Don Campbell
- Jun 03, 2016

Researchers in China have released details on the first robotic security guard aimed to stop riots.
- By Sydny Shepard
- Apr 29, 2016

A TV station in Baltimore is grateful for added security measures after bizarre standoff with costumed man.
- By Sydny Shepard
- Apr 29, 2016

The FBI was finally able to extract the data from the San Bernardino attacker’s iPhone, but was it worth the price?
- By Sydny Shepard
- Apr 22, 2016

Police in Midlothian, Texas are asking for the public’s help to identify the suspect in a bizarre murder case.
- By Sydny Shepard
- Apr 20, 2016

Microsoft filed a lawsuit against the U.S. Department of Justice taking a stand against the way federal agents routinely search its customers’ personal information in secret.
- By Sydny Shepard
- Apr 15, 2016

Coachella, a music festival in Indio, California, will be seeing an increase in security measures due to recent world events.
- By Sydny Shepard
- Apr 15, 2016

Fans of the college basketball tournament, March Madness, may need to pay special attention to the information they shared on the CBS Sports app and website during the popular event.
- By Sydny Shepard
- Apr 13, 2016

This year at ISC West in Las Vegas, there were some definite trends to be seen in the security industry.
- By Sydny Shepard
- Apr 12, 2016
The last day of ISC West saw some unexpected and innovative products
- By Matt Holden
- Apr 12, 2016

The Chicago Police Department will be arming officers in gang-plagued areas with body cameras that will continuously record
- By Sydny Shepard
- Apr 12, 2016
Day 2 of ISC West featured demonstrations and dealer relations
Day 1 of ISC West kicked off with some exciting innovation as well as some award winning products.
- By Matt Holden
- Apr 06, 2016

Messaging app, WhatsApp, has made a move to encrypt all messages sent and received on their platform.
- By Sydny Shepard
- Apr 06, 2016

First Indoor Drone Technology for Visitor Management Launching via Kisi Labs.

There going to be a ton of new products at this year’s ISC West show, especially internet driven devices.
- By Sydny Shepard
- Apr 04, 2016

Yes, the world has changed a lot over the last five years and now we’re facing the next big challenge: the Internet of Things (IoT), and how to get it right.
- By Thorsten Held
- Apr 01, 2016

As a camera views and records in 360 degrees, a circular, distorted image is produced, making it essential to process the image so that the human eye can comprehend the image easily.
- By Jumbi Edulbehram
- Apr 01, 2016
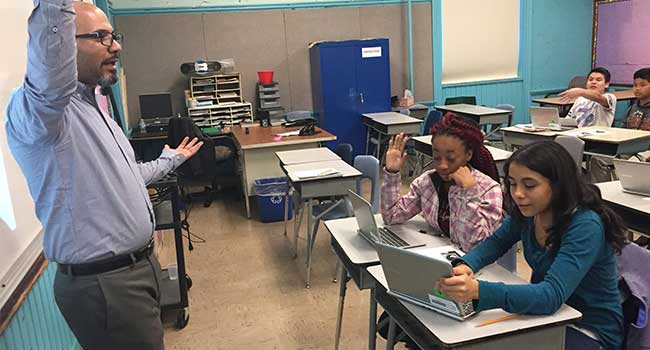
Citizen Schools mobilizes teams of educators and volunteers to lead real-world learning projects and provide academic support, helping students discover and achieve their dreams.