
Wrigley field will be opening two and a half hours early on Opening Day to allow fans to acclimate to the new security procedures.
- By Sydny Shepard
- Mar 25, 2016
ISC West attendees are invited to visit Orion Entrance Control Booth 12135 at ISC West to demo exciting new products.

There are many security risks that could come up by allowing citizens to vote online, but Utah is going to try it anyway.
- By Sydny Shepard
- Mar 22, 2016

Despite the fact that bad passwords are becoming a dying breed because of the immense security measures one must comply with in order to create a password to login to an account, sports fans have found a way to use their favorite games as terrible credentials.
- By Sydny Shepard
- Mar 21, 2016

New tests by German vehicle experts show that 24 cars from 19 different manufacturers are vulnerable to an “easily built” electronic device.
- By Sydny Shepard
- Mar 18, 2016

Hackers have adopted a number of attack methods, which include combinations of social engineering attacks, malicious mobile applications, phishing scams, and ransomware, to name a few.
- By Lance Mueller
- Mar 17, 2016

In order to cut down on the security risks and officer manpower involved during visitation hours, Faulkner County Jail will allow inmates to visit with friends and relatives by video.
- By Sydny Shepard
- Mar 14, 2016
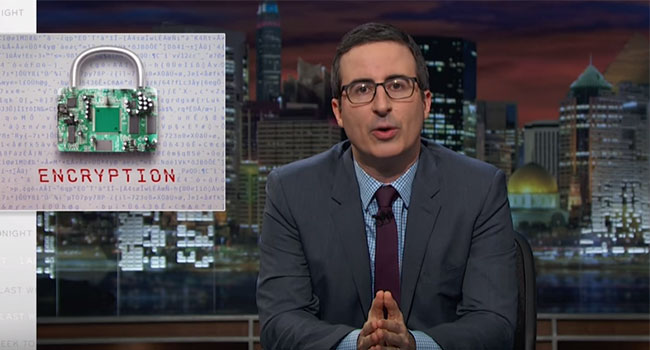
TV show host, John Oliver, used his platform on Last Week Tonight to help others understand the Apple vs. FBI debate.
- By Sydny Shepard
- Mar 14, 2016

Seven innocent participants will enter Clark County Jail undercover in order to help jail administration understand what really goes on in the facility.
- By Sydny Shepard
- Mar 11, 2016

Ford gives police cars a much needed upgrade, creating doors that cannot be penetrated by bullets.
- By Sydny Shepard
- Mar 11, 2016

Homeland Security officials want to prohibit the use of drones at the U.S. Open in an effort to prevent possible terrorist attacks.
- By Sydny Shepard
- Mar 09, 2016

The number of travelers is going up and the number of TSA screeners is going down, resulting in long lines at security check points.
- By Sydny Shepard
- Mar 07, 2016

Researchers say that police drones used for surveillance can be hacked with a rather inexpensive kit.
- By Sydny Shepard
- Mar 04, 2016

The Navy’s popular Blue Angels’ military base has remained unusually opened to the public – until now.
- By Sydny Shepard
- Mar 02, 2016

Ensuring your own safety is the most important aspect of working in Security. Body armor and other forms of protective clothing are vital pieces of equipment, and all Security Operatives (SOs) should be aware of their benefits.
- By Joshua Nash
- Mar 02, 2016

4K and Ultra High Definition (UHD) video content has approximately four times the resolution (4 times the number of actual pixels) of 1080p full HD. 1080p content has more than twice than 720p resolution. Add audio, metadata, potential multiple camera streams and you’ll soon be asking how you can deliver such high resolution over limited bandwidth connections or simply how to reduce storage costs.
- By Steve Surfaro
- Mar 02, 2016

New security methods were deployed for Tokyo’s marathon, including facial recognition and drones.
- By Sydny Shepard
- Mar 01, 2016

Over the past decade, high-tech devices, megapixels, Power over Ethernet, and many other new offerings and improvements have revolutionized the physical security landscape.
- By Fernando Pires
- Mar 01, 2016

Dallas train systems are beefing up their security by installing cameras with facial-recognition software.
- By Sydny Shepard
- Feb 19, 2016

The FBI is asking for Apple’s help to crack the code on an iPhone owned by one of the San Bernardino shooters.
- By Sydny Shepard
- Feb 17, 2016