When it comes to protecting transportation hubs, seaports have their own set of challenges.
- By Anthony Incorvati
- Feb 01, 2017

A group of gunman entered a mosque in Quebec and open fired killing six.
Bridge Safety and Security Bolstered with Key Management System

Following two shooting incidents that killed one and injured nine more, the city is planning new security measures on Bourbon Street.

Markeith Loyd was captured on Tuesday, January 17.

A gunman opened fire, shooting at least 12 people and killing five of them.
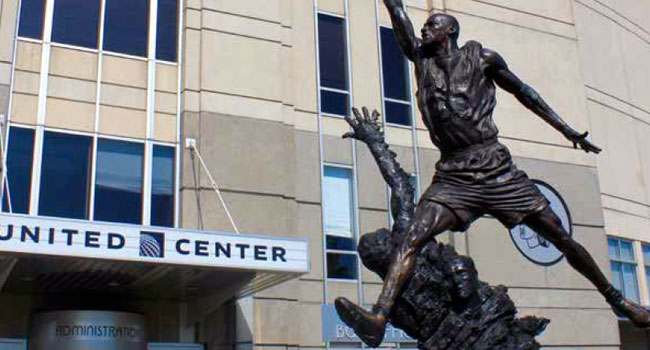
Frustrated with a faulty analog security setup, Chicago’s United Center set out to raise their technology standards and centralize operations through a network system.
- By Mark McCormack
- Jan 01, 2017

Electoral College voters will cast their ballots for President of the United States amid heightened security.

The suspect is in custody following an overnight standoff with police.

A 19-year-old “survivalist” was arrested after bringing in weapons to Trump Tower on Tuesday.

At least 10 were injured when a white supremacist group and counter-protesters clashed at a rally on the Sacramento Capitol steps Sunday, June 26.
- By Sydny Shepard
- Jun 27, 2016
It was critical for Ripon to deploy a comprehensive safety and security program that streamlined access management across the expansive campus.

Officials of VidCon, a conference that brings Social Network stars and their fans together, will see increased security in the wake of the shootings in Florida.
- By Sydny Shepard
- Jun 14, 2016

The Transportation Security Administration at airports around the country will be undergoing covert security tests over the summer.
- By Sydny Shepard
- Jun 08, 2016

Get the latest news on the security surrounding the Euro 2016 championship in France.
- By Sydny Shepard
- Jun 06, 2016

Researchers in China have released details on the first robotic security guard aimed to stop riots.
- By Sydny Shepard
- Apr 29, 2016

While some restaurant owners may see video surveillance as a “nice-to-have,” to improve security and deter theft, more owners are seeing their investment in surveillance pay off in surprising ways.
- By Douglas Wong
- Apr 21, 2016

Police in Midlothian, Texas are asking for the public’s help to identify the suspect in a bizarre murder case.
- By Sydny Shepard
- Apr 20, 2016

Afghan police are reporting an explosion that killed dozens and left hundreds wounded.
- By Sydny Shepard
- Apr 19, 2016

It’s been three years since a terrorist attack plagued the Boston Marathon, but authorities are not letting up on keeping the runners and spectators safe.
- By Sydny Shepard
- Apr 18, 2016