
There’s an old axiom that a good salesman could sell virtually anything to anybody—even if the item isn’t always the best fit for a need.
- By Patrick V. Fiel Sr.
- Jul 01, 2014

When most people think of school violence, they immediately think of school shootings. The media saturation that covers these shootings makes it unavoidable. however, school shootings are only the most extreme and rarest example of school violence.
- By Don Commare
- Jul 01, 2014

The International Energy Agency predicts that America will overtake Saudi Arabia as the world’s leading oil producer by 2017 and be a net oil exporter by 2030.
- By Anthony Incorvati
- Jul 01, 2014
Students, staff and instructors begin their day at a reasonable hour during a work day, but for security, time has no meaning.
- By Steve Surfaro
- Jul 01, 2014

Hospitals offer patients a controlled environment that encourages rapid healing protected from the outside world. Yet, hospitals are open to the public and subject to many of the same security threats as the world at large.
- By Courtney Mamuscia
- Jul 01, 2014

Crime doesn't discriminate against size; small businesses are typically most vulnerable with fewer resources to guard against it.
- By Scott McNulty
- Jun 17, 2014
Global Fusion Center offers manned, 24-7, real-time surveillance and security verification services for a variety of verticals.

When Rush University Medical Center incorporated wireless electronic locks throughout its new 375-bed-tower hospital building, it made installation easier and more cost-effective while providing greater flexibility to meet future security needs.
- By Karen Keating
- Apr 01, 2014

Two passengers who boarded disappearing Malaysia Airlines jet with stolen passports could have been identified by authorities within seconds possibly minutes.
- By Ginger Hill
- Mar 13, 2014

New hosted license plate recognition solution eliminates the need for dedicated IT infrastructure and minimizes deployment and maintenance costs.

It’s 2014 and time for a new way of thinking when it comes to security. It’s kind of like our five senses; we have each one for a reason, and they are all equally valuable.
- By Richard Brent
- Mar 01, 2014

Fashion and security collide to bring a new line of wearables to the market for personal safety.
- By Ginger Hill
- Feb 19, 2014
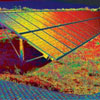
The remote solar field was pitch black, yet the thermal cameras detected movement by the fence and sent out an alarm. The officer on duty at Campus Safety took one look at the thermal images streaming onto the video monitor and realized the magnitude of the alert.
- By Fredrik Nilsson
- Dec 30, 2013

The shooting spree at Sandy Hook Elementary in December 2012 shattered the sleepy town of Newtown, Conn., and once again shattered America’s notions of what constitutes a safe place.
- By Vance Kozik
- Nov 01, 2013

The Penn-Harris-Madison (PHM) School Corporation exercises its security plan often, and to that end, they invite local law enforcement and their security provider, Honeywell Building Solutions, to participate in enforcement procedures, mock events and planning.
- By Ralph C. Jensen
- Nov 01, 2013

Mobility and efficiency makes remote monitoring an attractive option to maximize productivity.
- By Dave Poulin
- Oct 28, 2013
High-definition, megapixel cameras can cover larger areas with fewer cameras while delivering superior detail and improving overall security operations.
- By Scott Schafer
- Oct 01, 2013
Remote monitoring of critical infrastructure used to be very difficult, but thanks to available technologies, this task can be achieved with a fraction of the resources required in the past.
- By Matt S. Nelson
- Oct 01, 2013
Web and mobile clients take security operations to the next level of efficiency.

Remote situational awareness provides operators, security personnel and first responders with decision making data to appropriately and effectively respond to perceived threats.
- By Justin Thompson
- Aug 01, 2013