
Umberto Malesci explains what IoT is, what it does and gives real-world examples of IoT in action.
- By Ginger Hill
- May 29, 2015
Free software allows datacom professionals to download, manage, edit and print pdf reports in three easy steps.

Seemingly limitless system applications allows manufacturers to significantly increase capabilities of cameras and other devices.
- By Ronnie Pennington
- May 12, 2015
Low cost, feature rich with large backlit displays.
Security managers are more aware than ever that information security requires a layered approach with components addressing every point of intrusion on the corporate network.
- By Julie Olenski
- May 01, 2015

Now more than ever, major network vulnerabilities are making national and international news headlines.
- By Madeline Domma
- May 01, 2015
Throughout the world, security and screening for explosives is a vital service for numerous types of businesses and organizations—from package transport to government agencies and to financial institutions.
- By Randy Smith
- May 01, 2015
Increased security concerns, availability of IP networks, camera sprawl and improvement in video content analytics are all contributing to a rapid growth in the amount of video surveillance data that federal agencies are gathering today.
- By Michael Gallant
- May 01, 2015

The security industry is under attack by buzzwords, and the Internet of Things (IoT) is one of a few leading the assault.

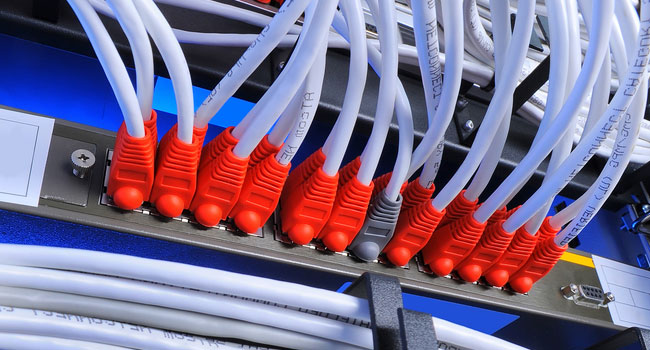
Are your physical security devices attached to the same network as your sensitive business data?
- By Vince Ricco
- May 01, 2015
Whenever I receive a cover story from Vince Ricco I listen, and I learn. I’ve known Vince for quite a while, and when he asks if your security devices are connected to your sensitive business data, it really makes you think.
- By Ralph C. Jensen
- May 01, 2015
Customers, channel partners, reps and industry friends and supporters recognize leader in wireless systems.
For exacting audio installation checks, designed to IEC651 and ANSI S1.4 standards.

For every organization, one of the first steps in providing safety and security is knowing at all times who is in the building. This is true for protecting people, property, or assets, and whether the building is a business, school, hospital or any other location.

Americans want to be safe and the FCC is helping. The FCC reserves valuable radio frequencies for public safety authorities that can be used for Ultra-Reliable wireless video surveillance.
- By Michael Derby
- Apr 01, 2015
Faster camera discovery, new camera integrations and more.
Company educating installers on the perils of using knock-off REELEX bulk wire cartons while vowing to continue to pursue measures against patent and trademark offenders.

New Jersey recently switched to digital testing, bringing a host of new security concerns with it.
- By Matt Holden
- Mar 17, 2015
Cable certifier, verifier and tester allow network administrators to confirm correct installation of copper and fiber network cabling and troubleshoot existing analog and IP video surveillance system installations.
When selecting a PoE switch for an IP surveillance network, system integrators should be aware that not all switches are created equal. PoE switch manufacturers offer a variety of different features that can impact functionality and pricing.
- By Steven Olen
- Mar 01, 2015