
Katz, who has been with ZKTeco since 2018, was promoted this month
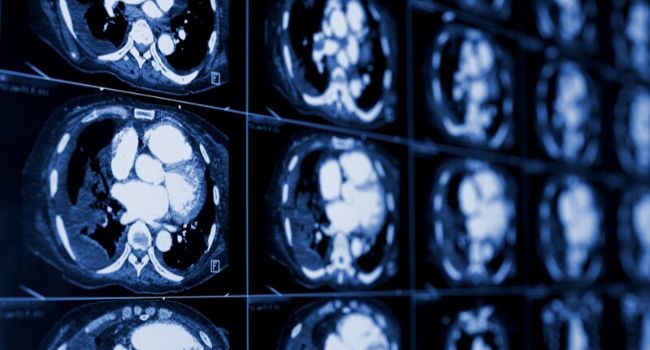
Some security experts and lawmakers have criticized the Department of Health and Human Services for failing to enforce privacy laws and fine organizations that did not protect patient records.
- By Haley Samsel
- Jan 14, 2020
“I look forward to working with the Board to help Mission 500 continue to grow and help those in need," O'Neil says

The bipartisan measure would allow parents to delete information collected by companies about their kids and raise the age of parental consent protection from 13 to 16.
- By Haley Samsel
- Jan 13, 2020

Weak passwords, insecure network services and a lack of secure update mechanisms top the list of risks for companies utilizing IoT technology.
- By Gilad David Maayan
- Jan 13, 2020

Airlines are also suspending flights to and from Iraq, Iran and other countries due to threats of missile attacks, one of which is suspected to have downed a Ukrainian passenger plane.
- By Haley Samsel
- Jan 10, 2020

The Metropolitan Transportation Authority maintains that it has not used facial recognition on riders, but privacy advocates want records related to the technology the agency purchased.
- By Haley Samsel
- Jan 10, 2020

Following the disclosure of several security issues, TikTok issued a patch to ensure that user privacy was protected.
- By Haley Samsel
- Jan 09, 2020

The advisory warned businesses about cyber attacks featuring cryptocurrency sites and spam campaigns impersonating government agencies.
- By Haley Samsel
- Jan 08, 2020

Technology advances have made security and access management more efficient.
- By James Barbour
- Jan 08, 2020

The department warned in an alert that Iran has a “robust cyber program” and can carry out attacks to temporarily disrupt critical infrastructure.
- By Haley Samsel
- Jan 07, 2020

The company has faced complaints, and a lawsuit, from customers that hackers were able to take over accounts and speak to children through the doorbell camera’s speaker.
- By Haley Samsel
- Jan 07, 2020
Ohio alarm monitoring and systems integration security company made announcement on Jan. 1
Sales manager oversees growth in Michigan, Illinois, Ohio and more
Network design considerations for video management are essential to ensuring system performance, data integrity, and threat mitigation. The challenge is that system integrators are confronted with a multitude of existing situations which often do not meet industry or manufacturer best-practice standards in today’s dynamic cybersecurity-centric world.
- By Evan Stuckless
- Jan 03, 2020

Can we imagine a new decade in which we protect our privacy and security while still maintaining innovation and freedom online?
- By Tyler Reguly
- Dec 30, 2019

Native Americans had the highest rates of false positives, while African-American women were most likely to be misidentified in a law enforcement database.
- By Haley Samsel
- Dec 24, 2019

Nearly half of Americans don’t believe that delivery companies are doing enough to prevent theft, but the survey respondents also aren’t willing to change their online shopping habits.
- By Haley Samsel
- Dec 24, 2019