
Four sets of steel bollards have been installed on Memphis' iconic Beale Street as part of a safety improvement plan.
- By Sydny Shepard
- Apr 25, 2019

When it comes to citizen safety, the police cameras in Indianapolis are meant to keep an eye on crime and help catch potential threats.
- By Sydny Shepard
- Apr 25, 2019
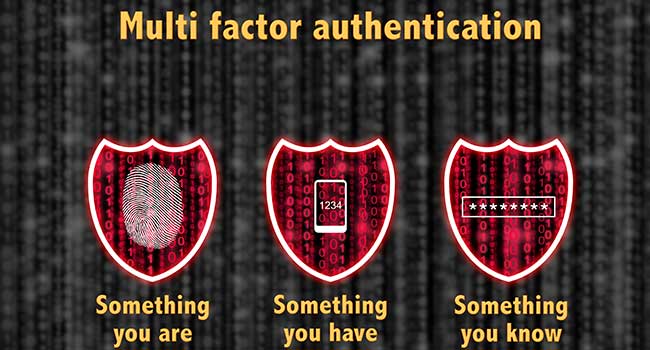
The U.S. Army is working toward adding more authentication measures to provide more options to access Army online resources while maintaining information technology system security.
- By Jessica Davis
- Apr 24, 2019

Beyond user privacy, we’ve seen GDPR impact companies in other ways.

The Chattanooga Police Department has 29 public safety cameras located around the city and plans to add more.
- By Jessica Davis
- Apr 24, 2019
Bee’ah’s sustainable headquarters will be infused with artificial intelligence
across systems and spaces, including a digital concierge for every occupant and visitor
Almost 300 people were killed and hundreds more were wounded in Sri Lanka on Easter Sunday in a series of coordinated attacks that struck three churches and three hotels.

EmCare Inc., a physician-staffing company, says a data breach has exposed personal information for about 31,000 patients
- By Jessica Davis
- Apr 23, 2019

- By Ralph C. Jensen
- Apr 22, 2019
All of your personal data can be easily accessible and vulnerable to hackers.
- By Susan Alexandra
- Apr 22, 2019

Due to the growing use of biometrics to counter security threats, the biometric technology market is expected to bloom over the next few years.
- By Sydny Shepard
- Apr 22, 2019

Chicago Metropolitan Metra transportation system launches a smartphone security app to report safety concerns.
- By Sydny Shepard
- Apr 22, 2019

Hospitals are often in the news due to data breaches, and email hacks are often the cause.
- By Kayla Matthews
- Apr 19, 2019
Arcules recently announced the addition of access control-as-a-service (ACaaS). Arcules now enables customers to centrally manage access control effectively across geographically dispersed business locations in a single, intuitive user interface
HID Global® recently introduced an augmented reality tool that innovates how integrators, installers and consultants deploy and use HID's access control products.
At ISC West, Bosch showcased how its offerings deliver value to integrators and end users by enhancing security, improving efficiency, and solving common challenges. Visitors to the booth will see intelligent solutions for vertical markets and new products and services that make systems easier to install and manage.
Dahua Technology has announced the addition of targeted vertical market solutions in the North American market