
As demand for controlled access communities continues to grow, so does the demand for secure and flexible access solutions.
- By Tom Potosnak
- Sep 01, 2018
In recent years, video surveillance has experienced a constant and rapid evolution of both technology and use cases for IP video in the traditional life safety and loss prevention worlds.
- By Vince Ricco
- Sep 01, 2018
One of the drivers for cloud adoption is that cloud security has expanded significantly. As confidence in these platforms grows, demand is rising to use trusted identity solutions in the cloud and benefit from its many advantages
- By Ian Lowe, Mark Robinton
- Sep 01, 2018
By definition, cash-in-transit (CIT) is the physical transfer of banknotes, coins, credit cards and items of value from one location to another.
- By Travis Ferry
- Sep 01, 2018

If you’re responsible for a medium or large-sized office, it’s more important than ever that you have access to a means of ensuring people’s safety, managing risks and fraud, and protecting property.
There is little question that the Southern U.S. border is porous; people stream into the United States at will. There is a great need for security; and the best technology should be used.
- By Ralph C. Jensen
- Sep 01, 2018

If you think your dealership isn’t conducive to outside pressures, ask the merchants of Smalltown, USA, about that new Walmart going up on the outskirts of the municipality.
- By Scott Lindley
- Sep 01, 2018
People are fallible creatures. As the saying goes, nobody’s perfect.
- By Jason Cronk
- Sep 01, 2018

Healthcare institutions face a variety of cybersecurity challenges, and the threats continue to grow and evolve. Hospitals are particularly vulnerable to data breaches and ransomware attacks because of the high value of healthcare data
- By Sheila Loy
- Sep 01, 2018

Google Chrome is largely considered one of the most security-conscious browsers, but recent headlines revealed some of its weaknesses.
- By David Pearson
- Sep 01, 2018
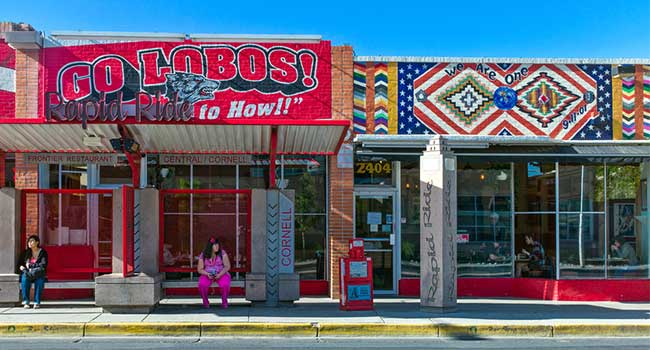
New Program puts 88 more cameras on Albuquerque’s streets.
- By Jordan Lutke
- Aug 31, 2018

A man defied security measures to kill his bedridden wife and himself, rattling hospital staff.
- By Jordan Lutke
- Aug 31, 2018

A man faces a criminal charge after police say he threatened to commit a mass shooting at a school using a 3D-printed gun.

The new tools will make it easier for users to protect their accounts.
- By Sydny Shepard
- Aug 30, 2018

The fall out from the Jacksonville shooting includes lawsuits, event cancellations and increased security for future gaming conventions.
- By Sydny Shepard
- Aug 29, 2018

The importance of communication in preventing and remediating cyberattacks
- By Vincent Geffray
- Aug 28, 2018