Hikvision USA announced that the Memphis Police Department has been honored with a Homeland Security Award as a result of their partnership with Hikvision.

Washington D.C. is offering rebates to those who install security cameras outside buildings.
- By Sydny Shepard
- Feb 18, 2016

Atlanta will see the installation of new security cameras and license plate readers as part of a security master plan.
- By Sydny Shepard
- Feb 18, 2016
‘Lean’ experienced, Campbell brings years of service experience to the company.

The FBI is asking for Apple’s help to crack the code on an iPhone owned by one of the San Bernardino shooters.
- By Sydny Shepard
- Feb 17, 2016
As a certified partner, OnSSI’s Ocularis 5 Video Management Software integrates with AMAG’s latest Symmetry V8 Access Control System.

A university in Tennessee is replacing old exterior doors and replacing them with door units centrally controlled by a locking system.
- By Sydny Shepard
- Feb 16, 2016
Transaction Delivers Significant Value to The ADT Corporation Stockholders and Provides Path for Future Growth of the Businesses Through the Combination of ADT and Protection 1
Hikvision® Canada, a leader in innovative video surveillance products and solutions, is pleased to announce that the company has been named Vendor of the Year by ADI Global Distribution.
ASSA ABLOY has successfully completed the acquisition of the ADAEZ Pro line of specialty door operators from EDMIT Industries.
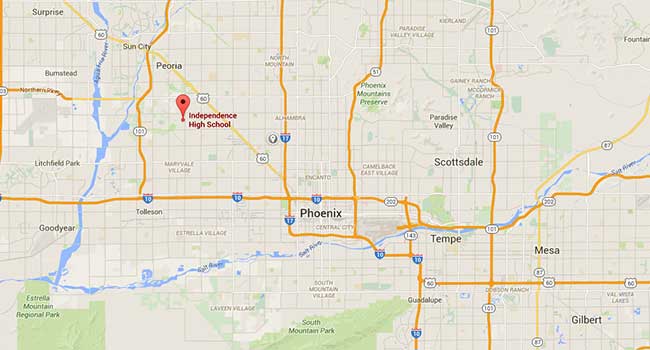
A school shooting in Arizona ends with two fatally shot students.
- By Sydny Shepard
- Feb 12, 2016

Congress seeks to bring parking garages within the secure perimeter of the House offices
- By Sydny Shepard
- Feb 12, 2016

In just a few short weeks, gunfire has claimed the lives of 6 police officers in 2016.
- By Sydny Shepard
- Feb 12, 2016

A riot broke out in Topo Chico prison in northern Mexico the morning of February 11 resulting in the death of at least 52 inmates.
- By Sydny Shepard
- Feb 11, 2016

Washington Metropolitan Area Transit Authority has recently seen a $3.6 million boost in security.
- By Sydny Shepard
- Feb 11, 2016
Bryon brings a record of sales success earned at Network Video Technologies, Panasonic, and Sony across a wide range of high technology products.

Director of National Intelligence speaks about which security threats the United States should be prepared for.
- By Sydny Shepard
- Feb 10, 2016
Jeff Smith has been promoted to District Manager of the DC Metro Area, while Erik Beck has been hired as the new General Manager for the Denver area.