Company continues aggressive expansion into European markets.
Dahua, Exar and Gen IV demonstrate Plug ‘n’ Play HDCVI products, anticipating the launch of HDCVI 2.0 compliance certification and the Alliance roadmap to 4K at ISC West.
Veteran climber will brave Mt. Everest to turn on lights, operate locks, and open garage doors to prove the reliability of devices from anywhere.
Attendees able to experience latest electronic access control solutions by touring the Intelligent Openings Showroom.
New 6K and 7K cameras join the family of 4K and 5K HD Pro cameras.
Company experiences increase in demand for Immix software platform in enterprise and central station markets.
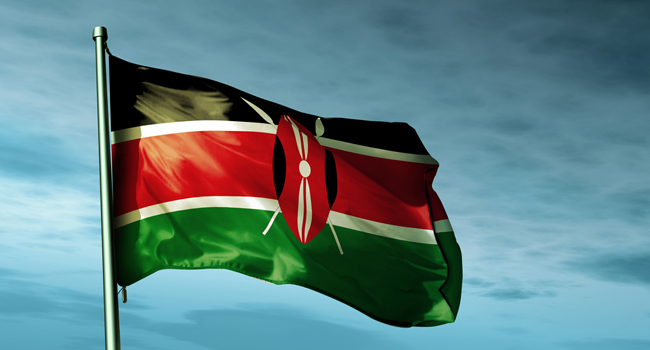
Students marched the Kenyan capital after gunmen killed nearly 150 people.
- By Matt Holden
- Apr 07, 2015
New telephone entry line to be unveiled at trade show in April.
Models available up to 18TB.
Offers high-performance and the ability to cope with any outdoor environment with new vandal-proof, IP67-rated enclosure.
Provides security infrastructure to manage and govern access to secure sections of airports by employees and contractors.
Platform brings together identity management, access control, alarm management and video management combined with situational awareness.

With a $900 million investment to fight terrorism, government agency mostly arrests for immigration violations.
- By Ginger Hill
- Apr 06, 2015

20-year-old Claudio Duran was arrested after bypassing a security checkpoint at JFK International Airport.
- By Matt Holden
- Apr 06, 2015
Salient Systems has strengthened its partnership with AMAG Technology beyond the long-standing deep integration of CompleteView VMS and Symmetry access control. AMAG will offer Salient's CompleteView Video Management System, PowerProtect NVR Server Platforms and TouchView Mobile Video Apps under the Symmetry™ brand.
The Security Industry Association (SIA) and ISC West are pleased to announce that SIA Education@ISC has been accepted into the (ISC)2 Official Continuing Professional Education (CPE) Submitter Program.
VITEK Industrial, a manufacturer of high quality and affordable video surveillance products, will showcase the latest from On Cue, Alpha, ENVI, and more, at ISC West Las Vegas — the largest physical security trade show in North America.
Offices close to PBI Airport and the growing downtown West Palm Beach, Florida for added convenience.