Allied Universal is announcing that it is providing Truckers Against Trafficking (TAT) with an online video training to the company’s more than 300,000 security professionals.
Eagle Eye Networks has announced record Q1 2021 revenue growth, and greater than 85 percent year-over-year revenue growth in 2020.

Vivint has agreed to pay a $20 million settlement from allegations that the company failed to use credit reports properly to help unqualified customers to obtain financing for products and services.
- By Ralph C. Jensen
- May 04, 2021
Open Options continues to build upon its commitment to innovation with the launch of Fusion X. This new web-based access control software includes all the benefits of the robust DNA Fusion platform but requires no software installation, or dedicated PC required.

This past year has seen a shift for organizations in everything from how they have operated, to the increase of digital transformation. However, current security and network solutions have failed to effectively meet the evolving needs of today’s digital businesses.
- By Michael Wood
- May 03, 2021
Vector Firm is pleased to welcome Gannon Switzer as vice president of Sales Management Consulting.
Securitas Electronic Security leverages FEMSS expertise and footprint to expand focus on local, mid-size businesses
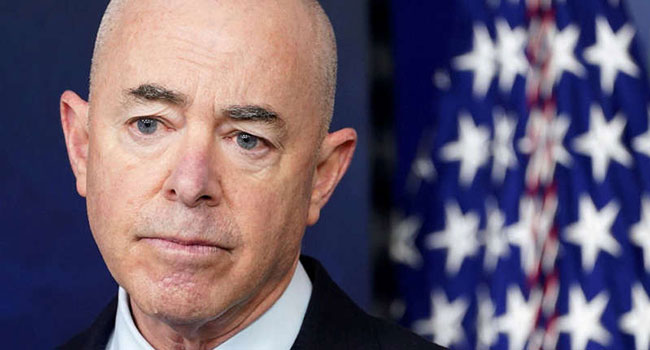
DHS Secretary Alejandro Mayorkas has launched an internal probe "to address the threat of domestic violent extremism within the Department of Homeland Security," according to a letter he wrote to all DHS employees.
Acre has announced the acquisition of TDS based in Dublin, Ireland.
BCDVideo has announced that it has partnered with Wasabi, the hot cloud storage company for video surveillance storage in the cloud.